Why Integrate THOR into Microsoft Defender ATP
While Microsoft Defender ATP fully plays off its strength in detecting live attacks, suspicious process starts and network connections, THOR shines as a live forensic scanner that scans the local filesystem, registry, logs and other elements for traces of hacking activity.
While Microsoft Defender ATP features a forensic package collection that retrieves elements from a remote system, THOR scans these elements on the remote system, applying more than 10,000 hand-written YARA rules and thousands of filename, C2, hash, mutex and named pipe IOCs to them. This live forensic scan reduces the work of your forensic analysts to a minimum and generates results as fast as possible for you to react in a timely manner.
THOR extends Microsoft Defender ATP’s real-time monitoring by intense local scans to allow a full on-demand compromise assessment.
Deployment Options
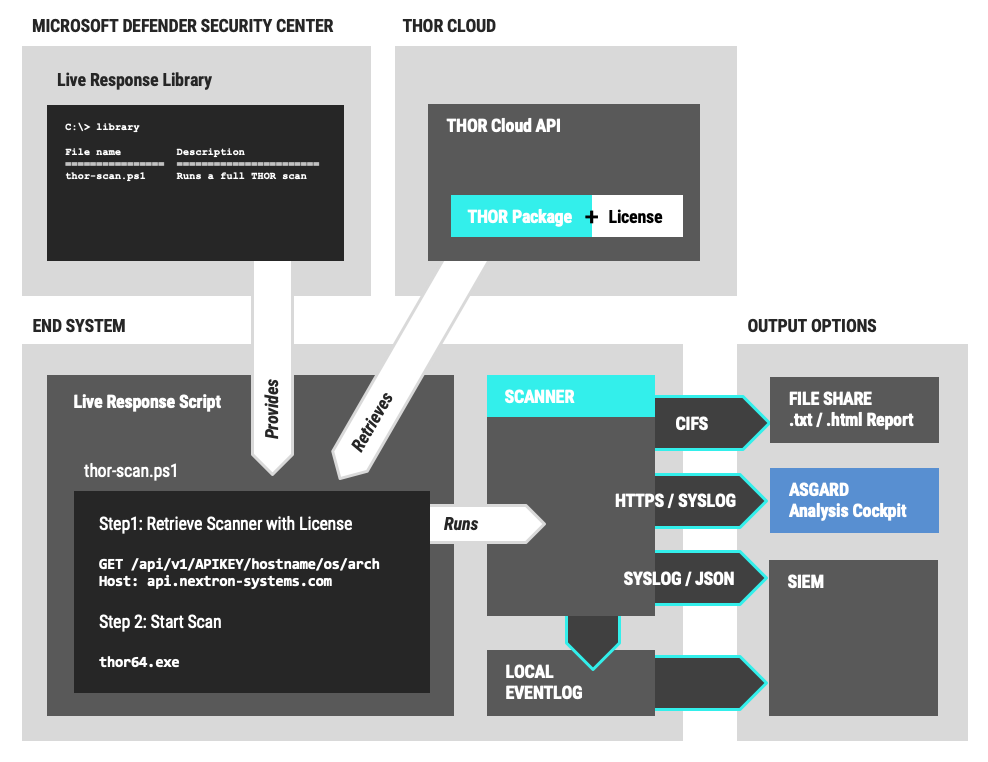
Due to the fact that both Microsoft Defender ATP and THOR are very flexible and open products, the integration is no one-lane road with a single possible solution. Depending on the network size, segmentation and available 3rd party solutions like a SIEM the integration allows and requires different setups.
This blog post starts with an example use case and then outlines many of these setup options.

Live Response Scripts
The Microsoft Defender Security Center allows us to upload PowerShell scripts into a so called “live response library”, which is available on the endpoint during “live response” sessions.
These scripts allow us to facilitate the download and execution of THOR on the endpoint.
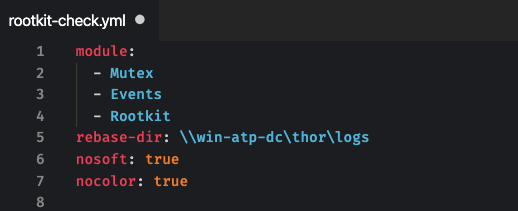
There are two ways to implement different scan modes and parameters. THOR has numerous command line options, which can be passed either as parameters of the PowerShell scripts or predefined in YAML config files.
Example: Turla Malware
We’ll use a simple demo script that contains a path to a file share providing the THOR package.

It uses a config file named “rootkit-check.yml”, which is located in the program folder on the file share. It activates 3 rootkit related modules, sets the path for all output files as rebase-dir and deactivates some features.
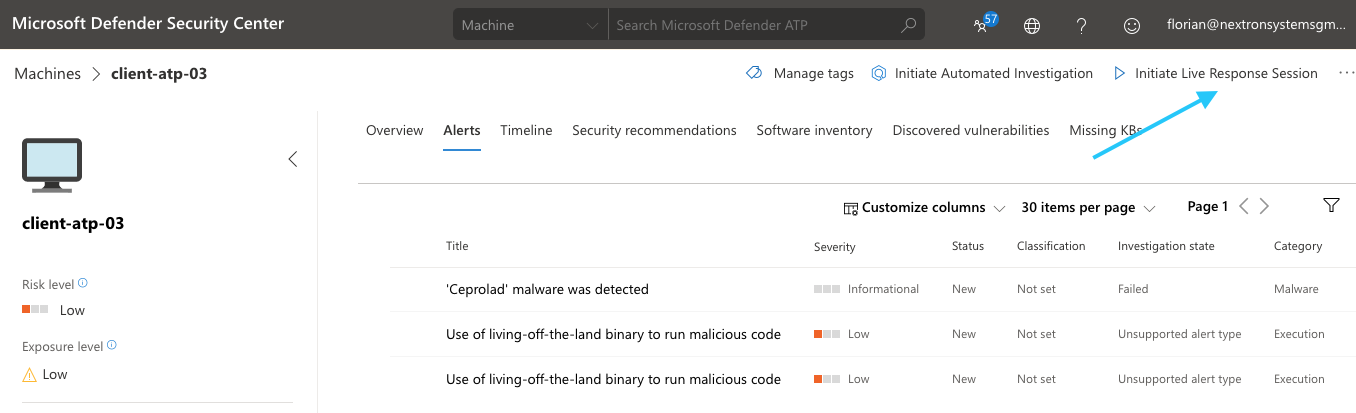
We upload that script into a live response session to investigate suspicious behaviour of a workstation that showed several alerts regarding a malware and the use of a “living-off-the-land” binary to run malicious code.
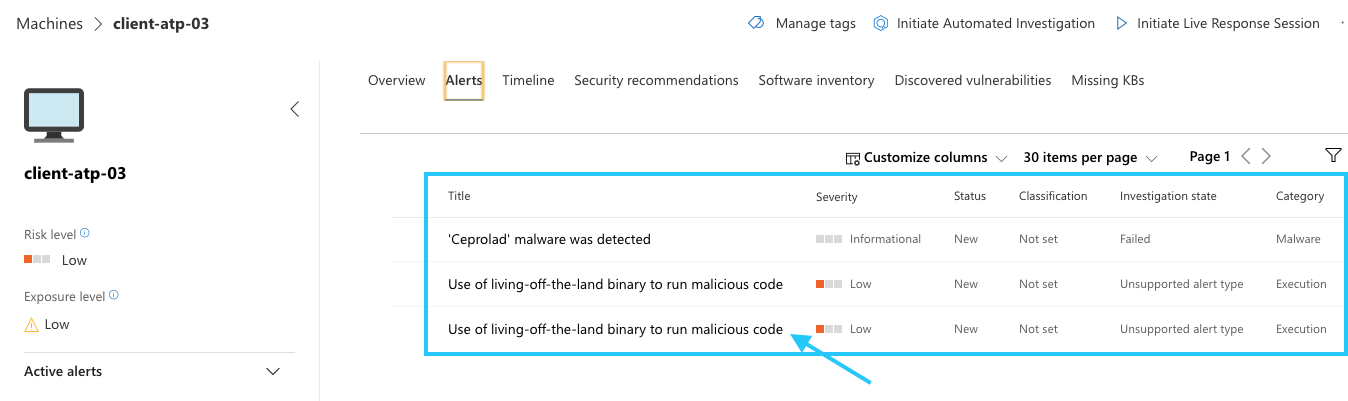
The details reveal that the use of certutil.exe triggered the alert.
We can see other commands like tasklist, net and netstat, which are often used in reconnaissance scripts, executed in the context of a user named “admin”.
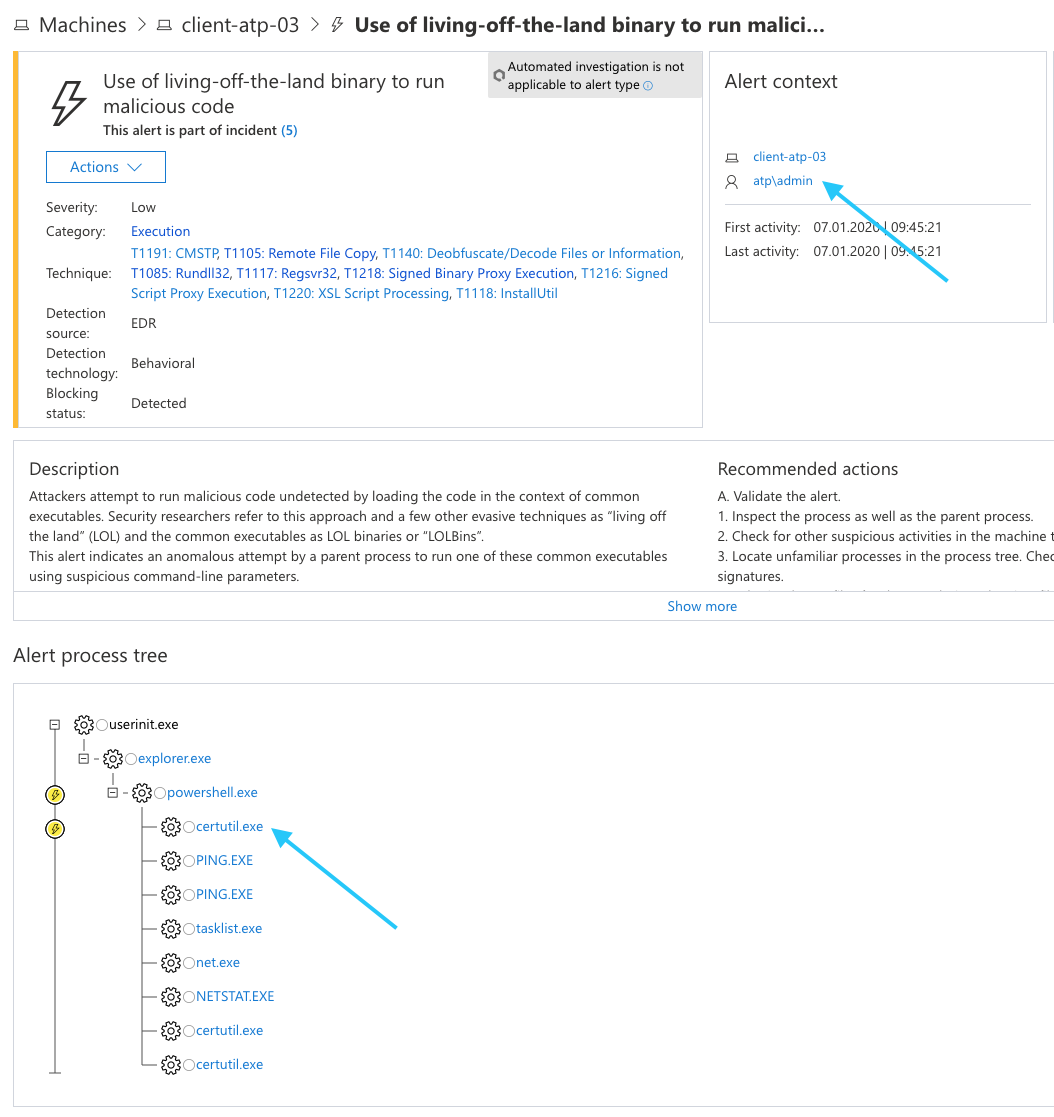
We start a “Live Response Session” for further live forensic investigations with the help of THOR.
Since this is our first investigation with that specific script, we have to upload it to the live response library.
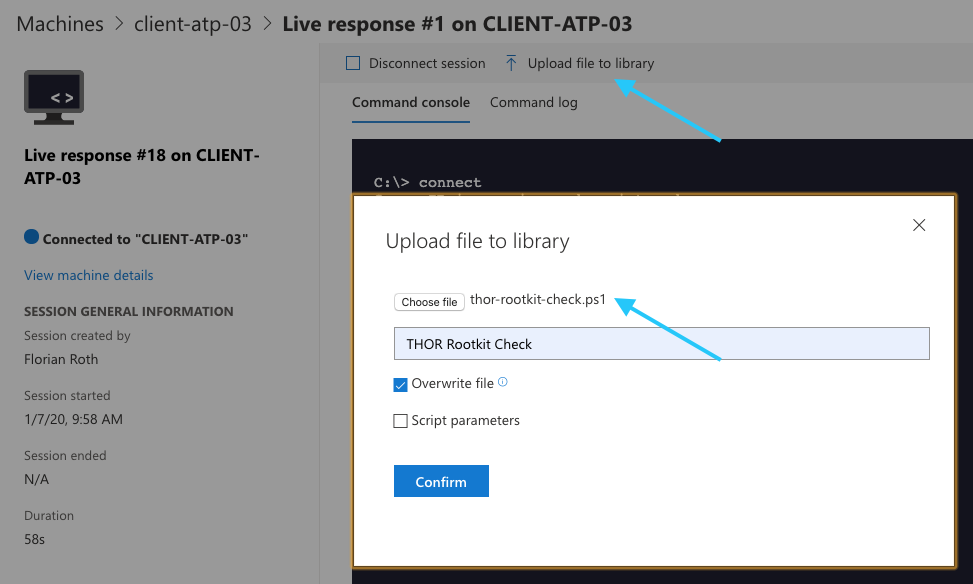
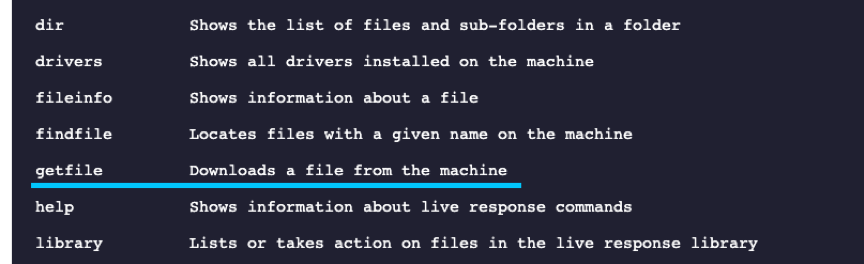
We can then verify the upload using the “library” command and run the script from the command line.
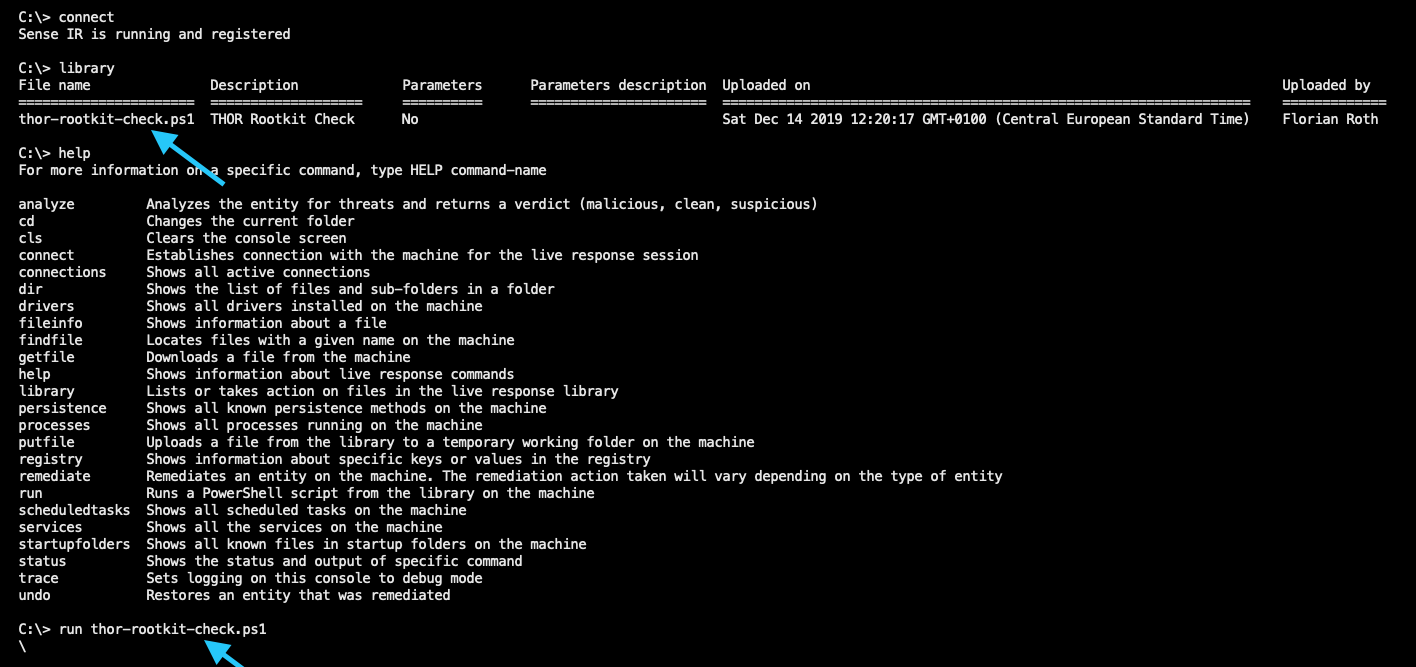
It takes about a minute to complete the Rootkit check.
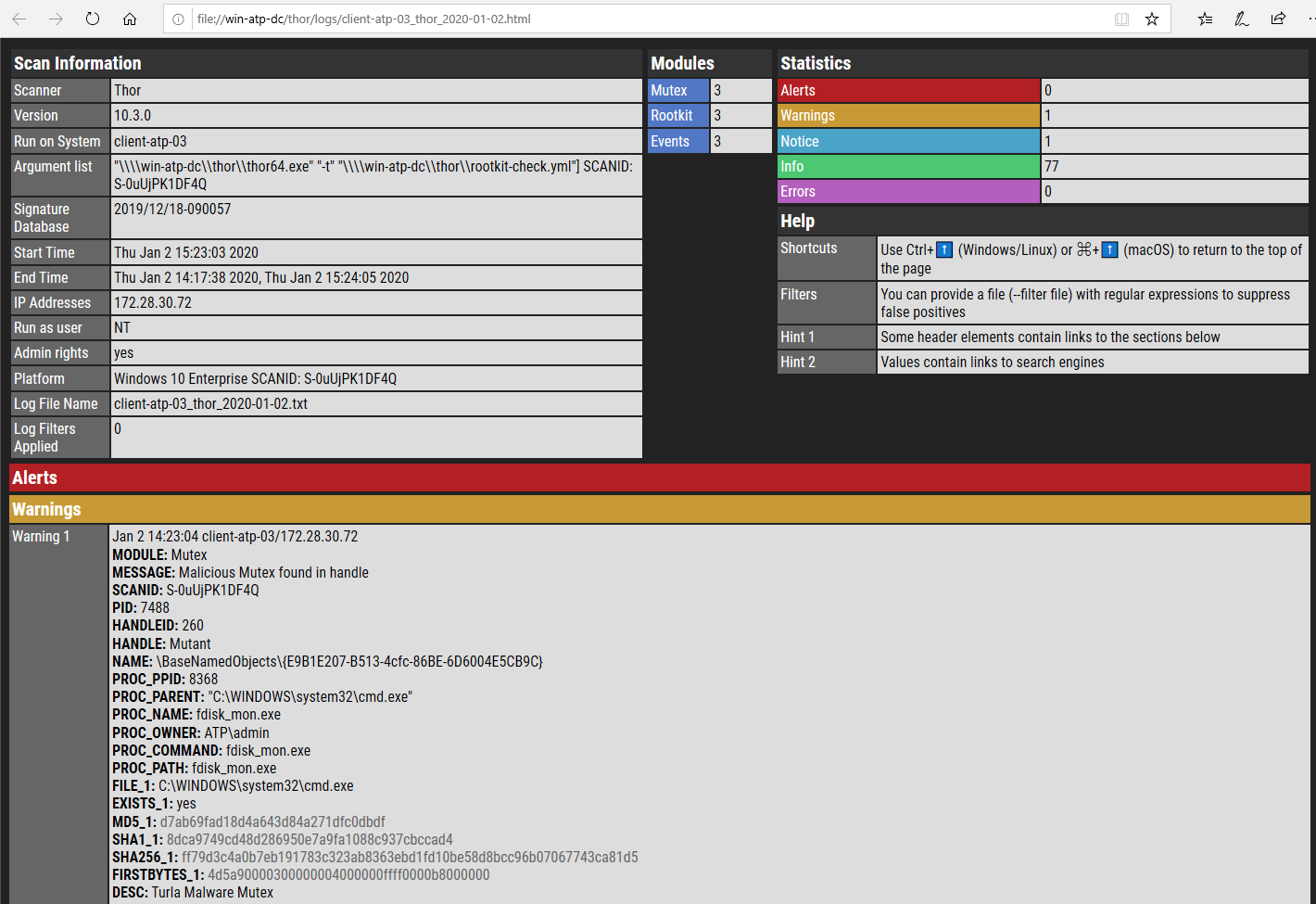
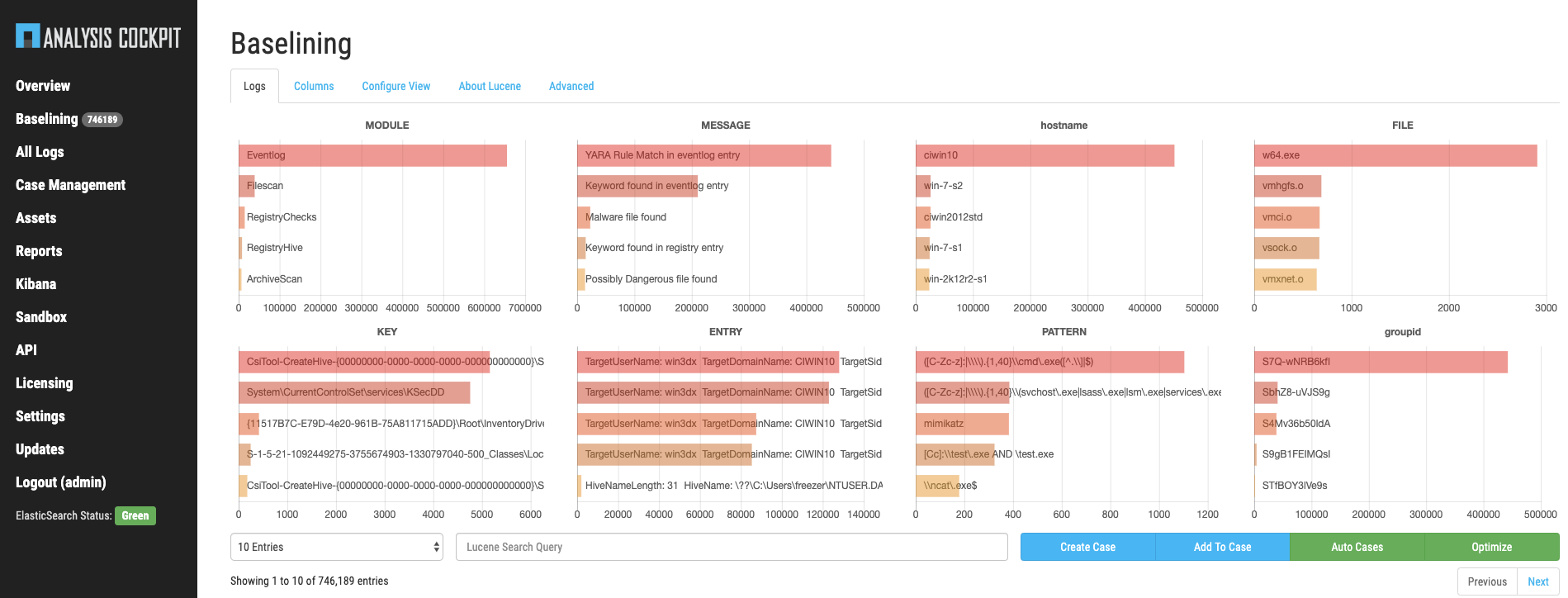
THOR recognized a malicious mutex used by Turla malware and gives further information on the related process and process binary, which can be used for additional verification of the threat.
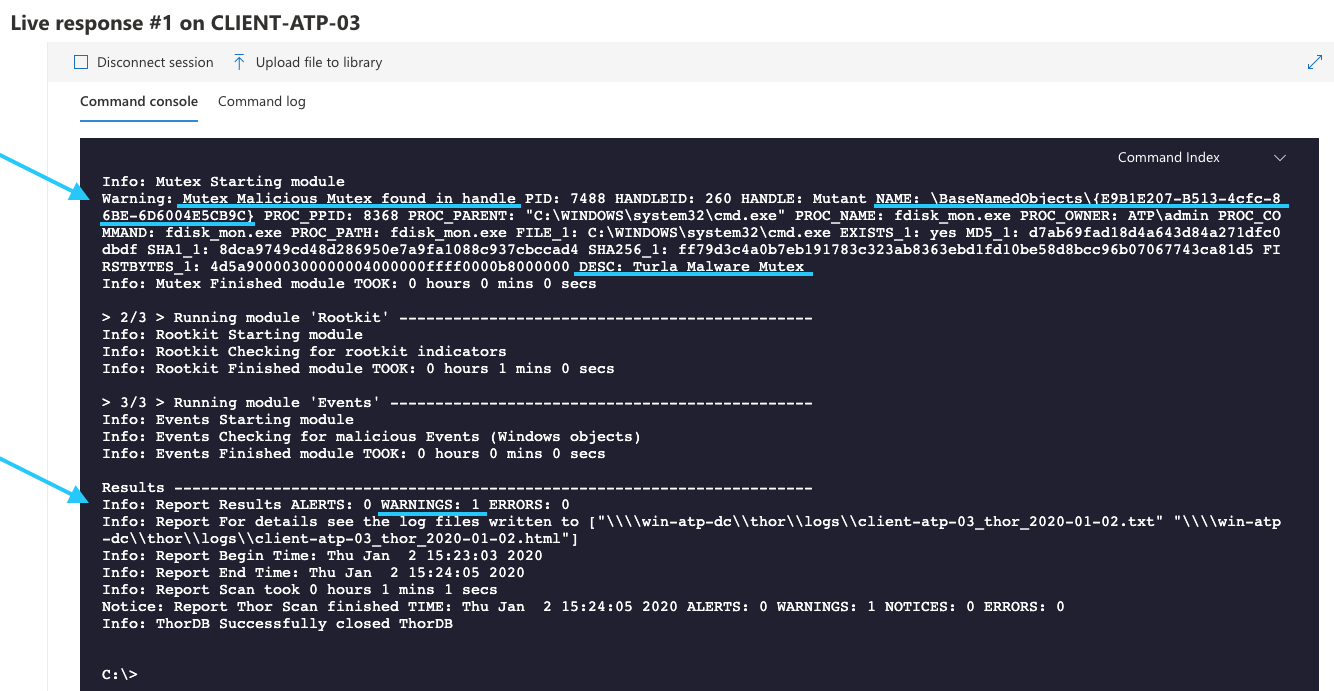
The HTML report and text log file have been saved back to the file share.
Other Setup Options
Scanner Provisioning
In this chapter we describe different methods to provide a THOR package to an end system during live response investigations.
Option A: File Share
The complete THOR package including binaries and signatures can be provided on a network share. This network share should be read-only to avoid that attackers notice the activity and manipulate the program or signatures on the file share.
Advantages:
- Quick setup
- Only a file server is needed
Disadvantages:
- Requires SMB/CIFS connection from end system to file share
- Scanner / signature updates must be scripted (thor-util.exe)
- Manual license generation (in Nextron’s customer portal) or expensive IR license (not host-based)
Option B: ASGARD Management Center
The central management platform ASGARD Management Center is hardened Debian-based soft appliance that serves as software repository and licensing server in our use case.
The PowerShell scripts in the script library can retrieve THOR packages via HTTPS from the ASGARD Management Center.
Advantages:
- HTTPS download of THOR packages
- Integrated licensing
- Automatic scanner and signature updates
Disadvantages:
- Additional server system (VM; maintenance)
Option C: THOR via Script Library as SFX
The complete THOR program folder can be packaged into a self-extracting & executing archive (SFX), which could then be uploaded into the “live response library”. It could then be executed right from the script library (run) or uploaded to the end system (put).
Advantages:
- No servers needed
- Microsoft Defender ATP native solution
Disadvantages:
- Scanner / signature updates and SFX creation must be scripted on an analyst system (thor-util.exe)
- Manual license generation (in Nextron’s customer portal) or expensive IR license (not host-based)
Output Options
The results of the scans can be stored and transmitted to different locations.
Option A: Log and Report on File Share
THOR writes a log file in real-time during the scan and renders an HTML report at the end of the scan. Users can set an output directory other than the working directory for all output files with the “–rebase-dir” parameter.
This output folder can be a file share, e.g. “\\server\share”.
Analysts can check the log file during the scan, which takes between minutes and hours to complete.
Advantages:
- Only a file server required
Disadvantages:
- Requires access to file share from the end system (SMB/CIFS)
- File share must be writable (possible manipulation by the attackers)
Option B: SYSLOG, JSON or CEF to SIEM
THOR can send the logs via SYSLOG (UDP, TCP, TCP+SSL, CEF) or in JSON (UDP, TCP, TCP+SSL) to a remote SIEM or log management system.
Advantages:
- Integrates into existing solution and processes
Disadvantages:
- Requires SIEM system and some base-lining
- Requires connection to port 514 from end system to SIEM system
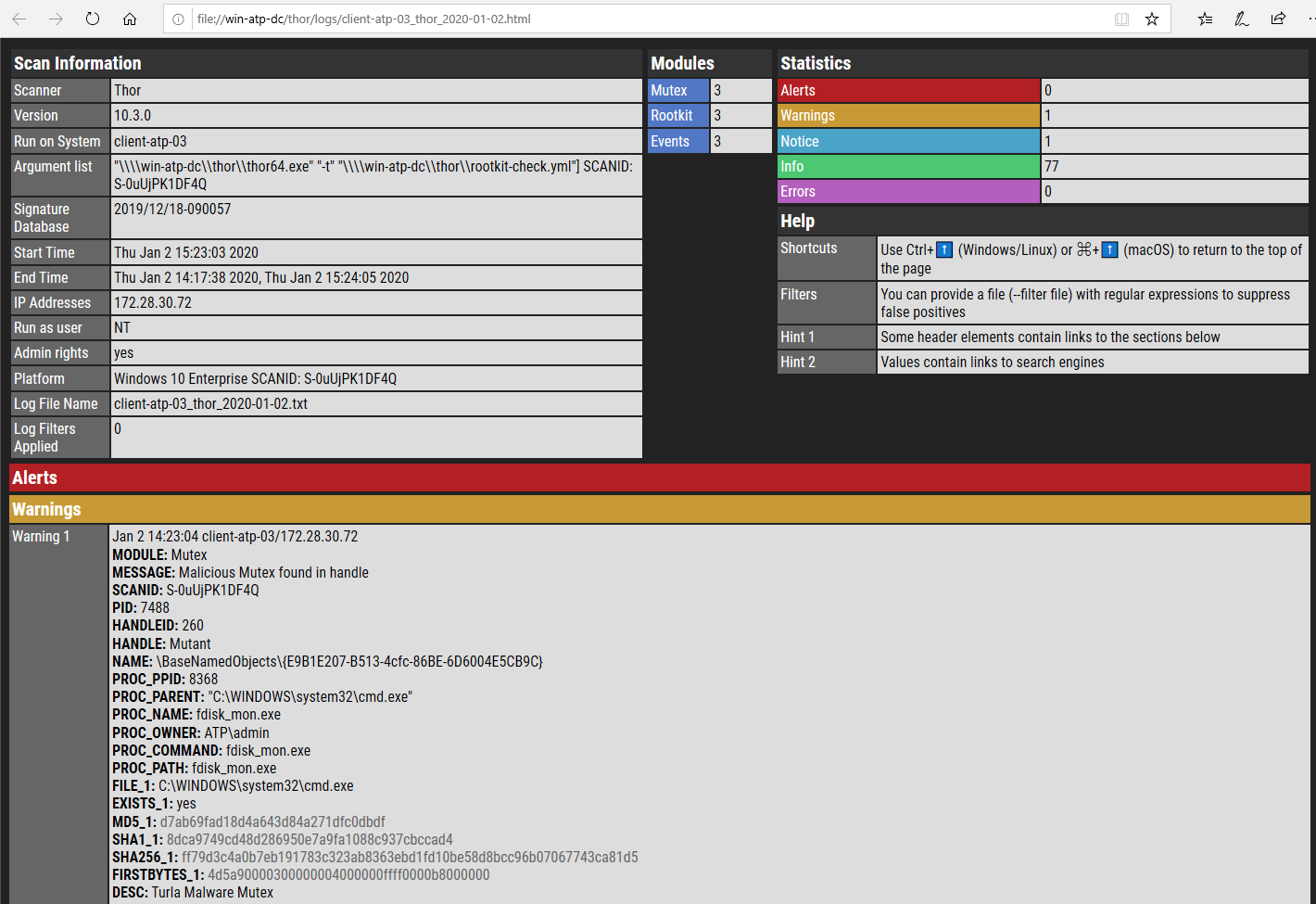
Option C: SYSLOG, JSON or CEF to ASGARD Analysis Cockpit
ASGARD Analysis Cockpit is the optimized log analysis platform (soft appliance) to process, baseline and forward THOR logs.
It most relevant features in this use case are:
- Base-lining and central false positive filtering
- Event forwarding of filtered events
ASGARD Analysis Cockpit already has several options to create alerts for incoming logs.

Advantages:
- Optimal THOR log base-lining and forwarding of relevant events only
Disadvantages:
- Additional server system (VM; maintenance)
- Requires connection to port 514 from end system to Analysis Cockpit
Option D: Local Eventlog
THOR can be instructed to log to the local Windows Eventlog with the “—eventlog” command line parameter. Customers that already forward their Windows Application Eventlog to a central SIEM could then use the existing integration and analyze the THOR events in their SIEM.
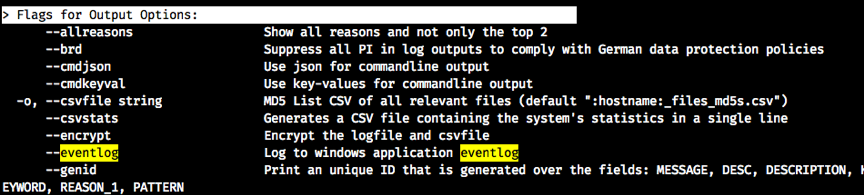
Advantages:
- Integrates into existing security monitoring
- No additional open port needed
Disadvantages:
- Requires SIEM system and some base-lining
Option E: Live Response – “getfile”
Local log files that were written to the working directory can be retrieved with the “getfile” command.
Advantages:
- Integrates into analyst workflow
- No additional open port needed
Disadvantages:
- Files could be left on the end system
(causing false positives in other products; in plain sight for attackers)
Future Integrations
This chapter contains an outlook on expected future integrations based on upcoming features and APIs.
Sample Collection
The Microsoft Defender ATP API allows to fetch a certain file from a remote system. Similar to the alerting mechanisms via Webhooks in ASGARD Analysis Cockpit, users will be able to fetch any suspicious or malicious file reported by THOR with a given minimum threat score using the Microsoft Defender ATP API.
THOR Cloud
The upcoming cloud based version of our licensing and download server, which is currently integrated into our customer portal, will be able to serve THOR packages that contain an integrated license for the host which is supposed to be scanned.
This way, you will we be able to run a PowerShell script from the live response library that downloads an up-to-date THOR package with a valid license file right from the new online service and don’t need a local ASGARD server that provides the THOR packages and licenses.