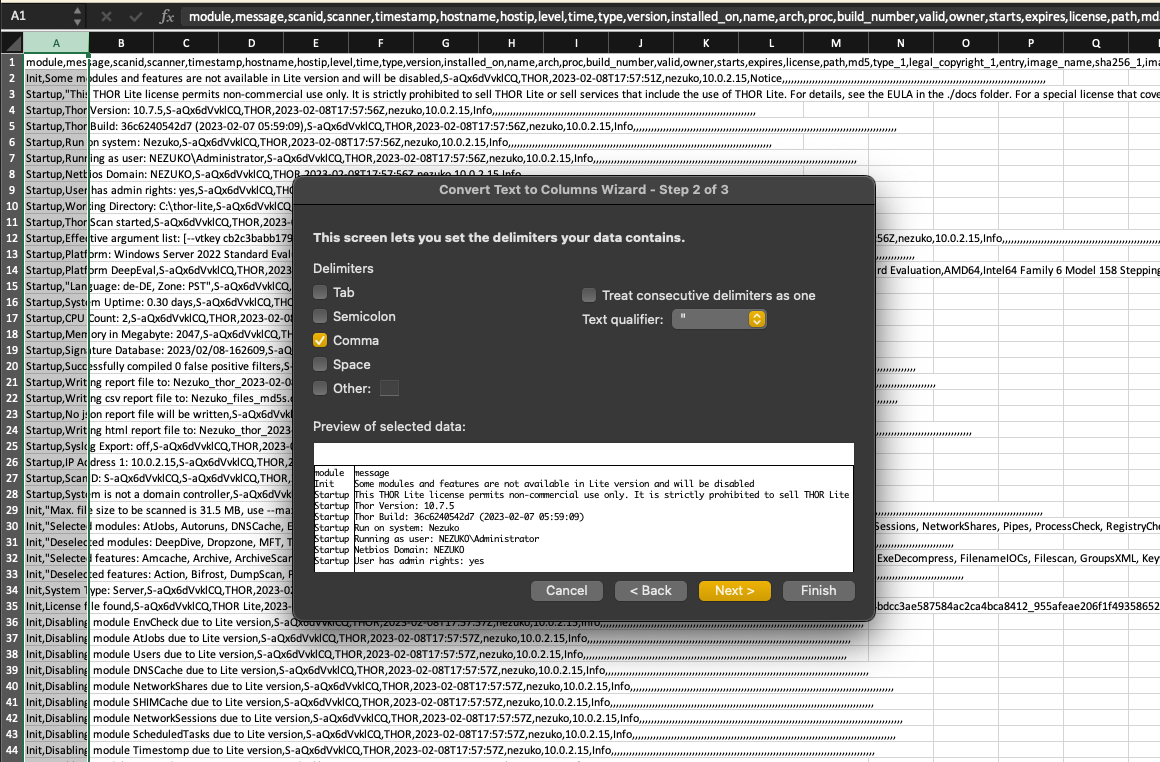
We are excited to announce that the upcoming version 1.11 our tool, THOR Util, now has the capability to convert log output files from both the default and JSON format into CSV files. This new feature will make it easier for users to analyze their log data and extract the information they need.
This will save time and increase productivity, as users will no longer need to manually parse and extract data from their log files.
We recommend taking a look at Modern CSV as alternative to Microsoft Excel for this kind of task.
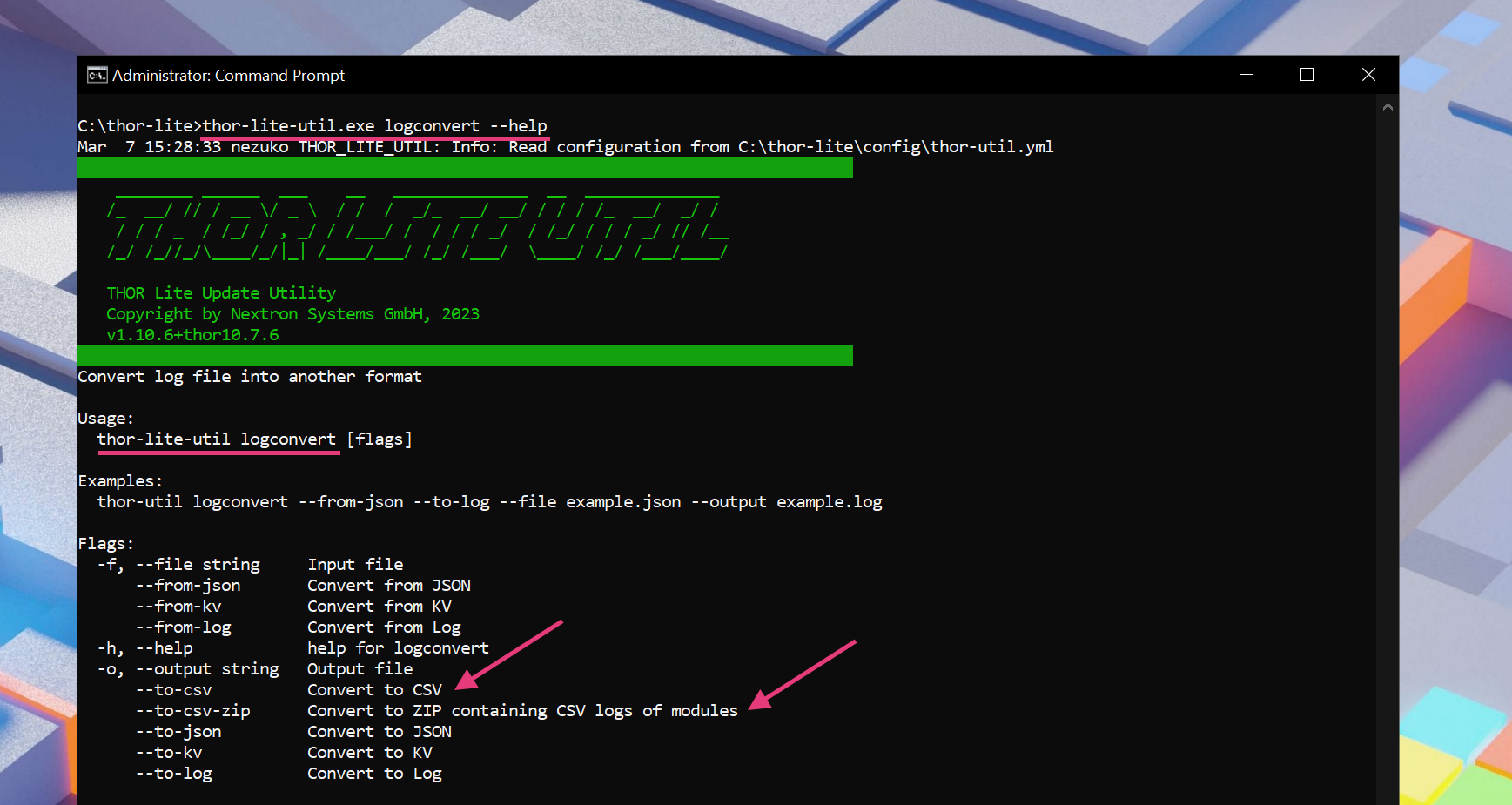

THOR Util has many more functions to post-process THOR logs, and this new feature further expands its capabilities.
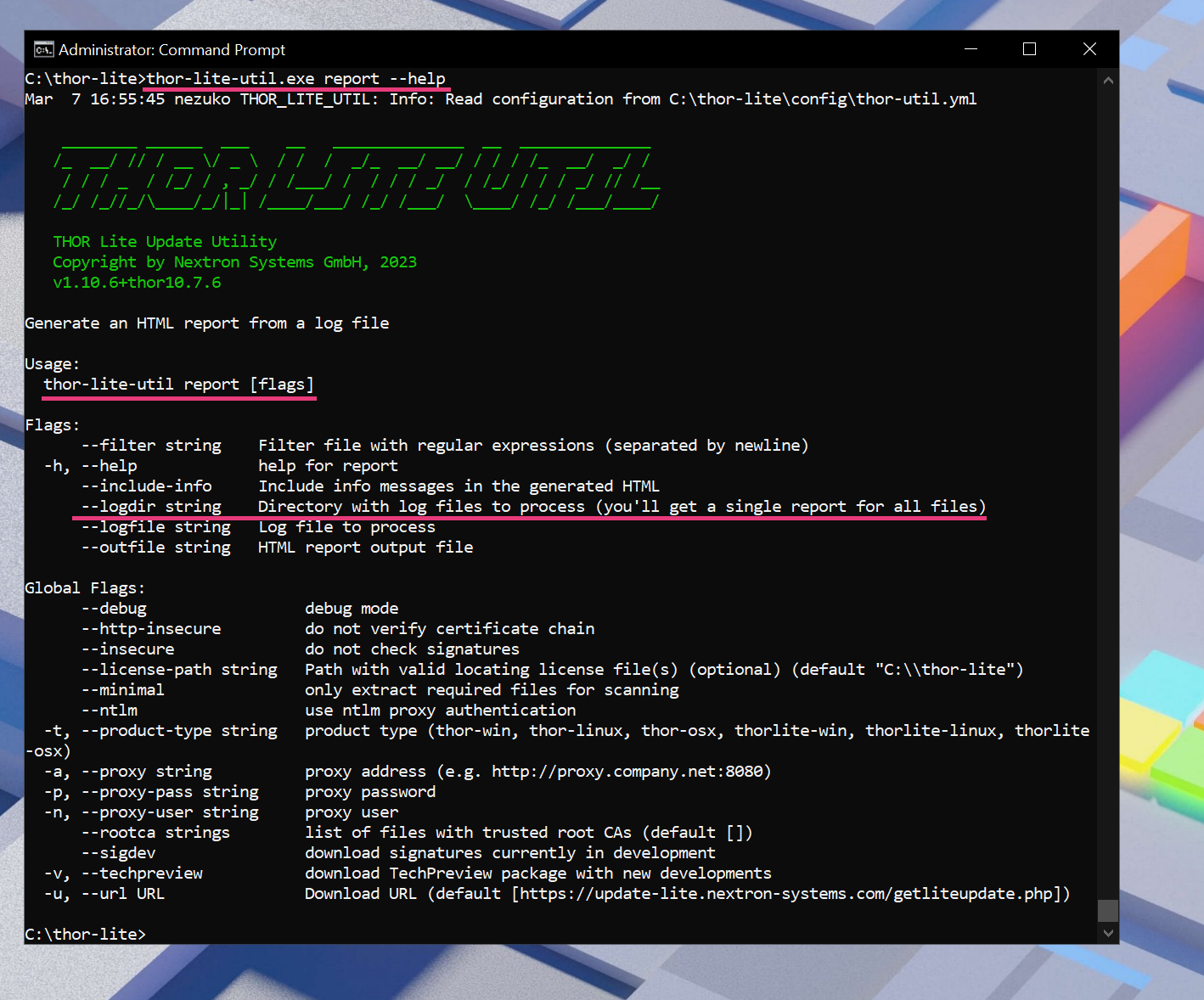
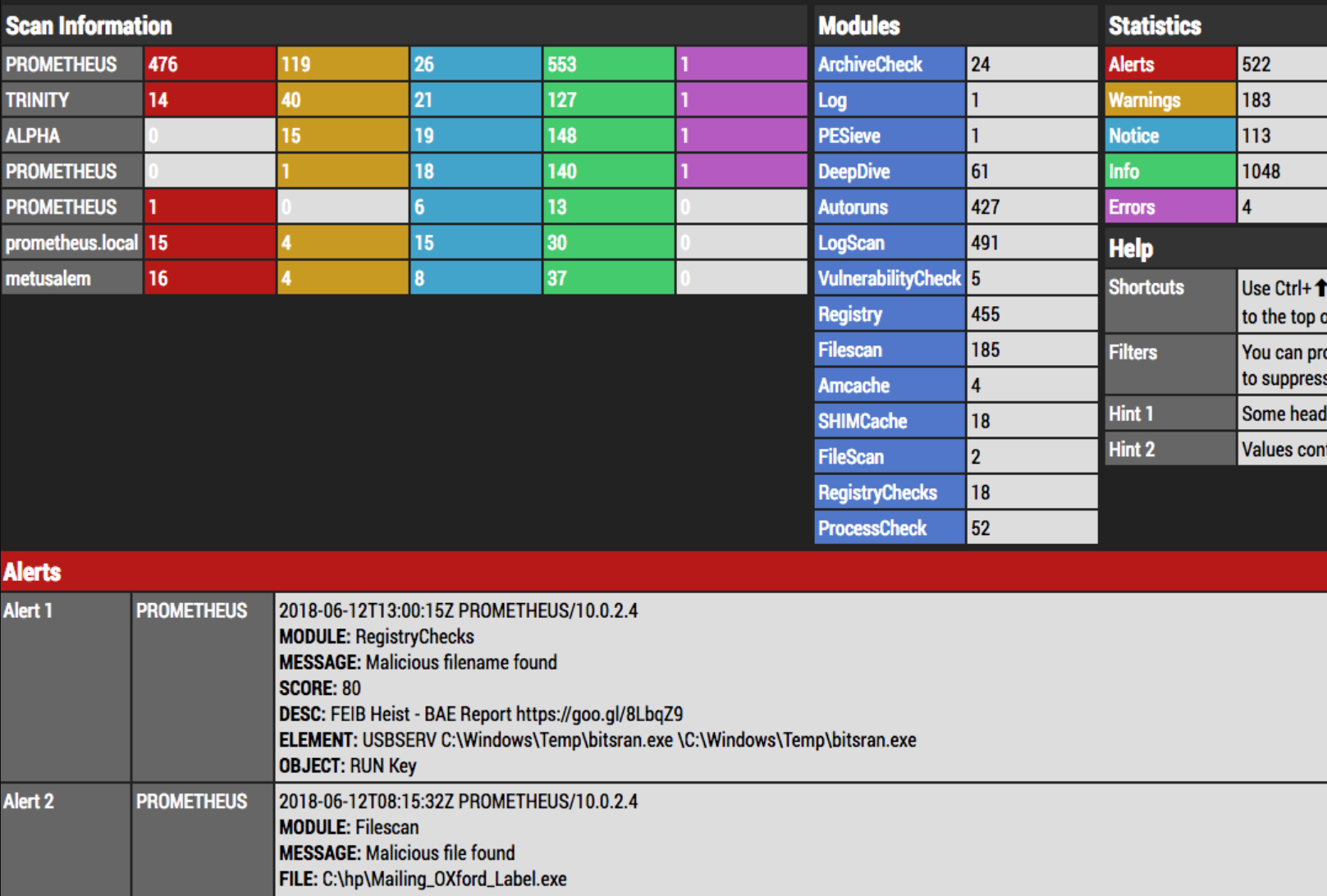
E.g. Did you know that you can use the “report” function to generate a single combined HTML report for a set of log files from different end systems?
You can find more information on THOR Util and its features here.
The release is planned for calendar week 11, 2023.