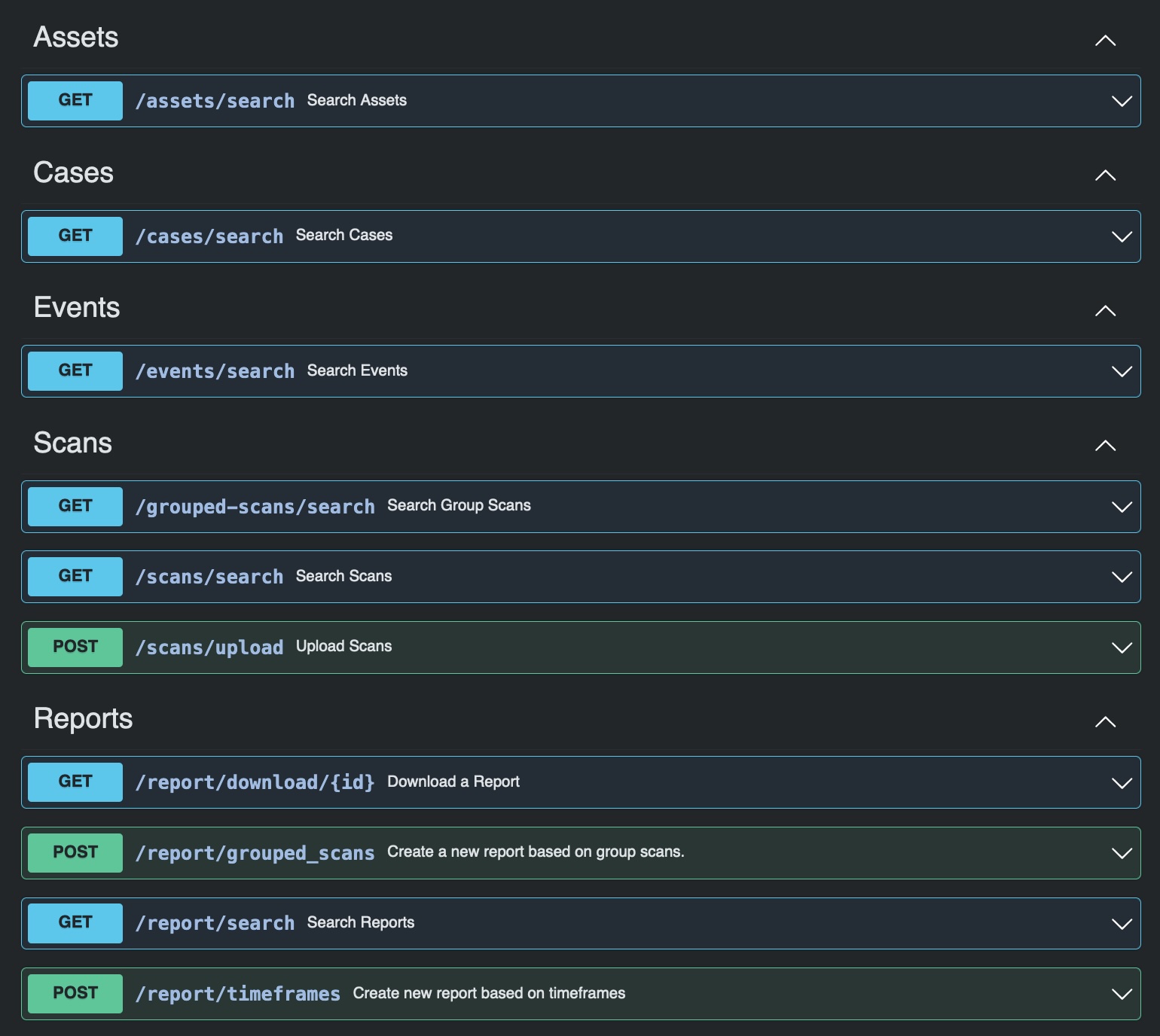
The Analysis Cockpit also features an integrated and highly configurable case management system that lets multiple analysts collaborate on the same investigation while ensuring the intended workflow progresses. Just like the ASGARD Management Center the Analysis Cockpit features a rich set of APIs that lets you connect to enterprise ticketing-systems, Sandboxes, CMDBs, SOAR Systems, threat intel platforms and literally any security device you may have in place.
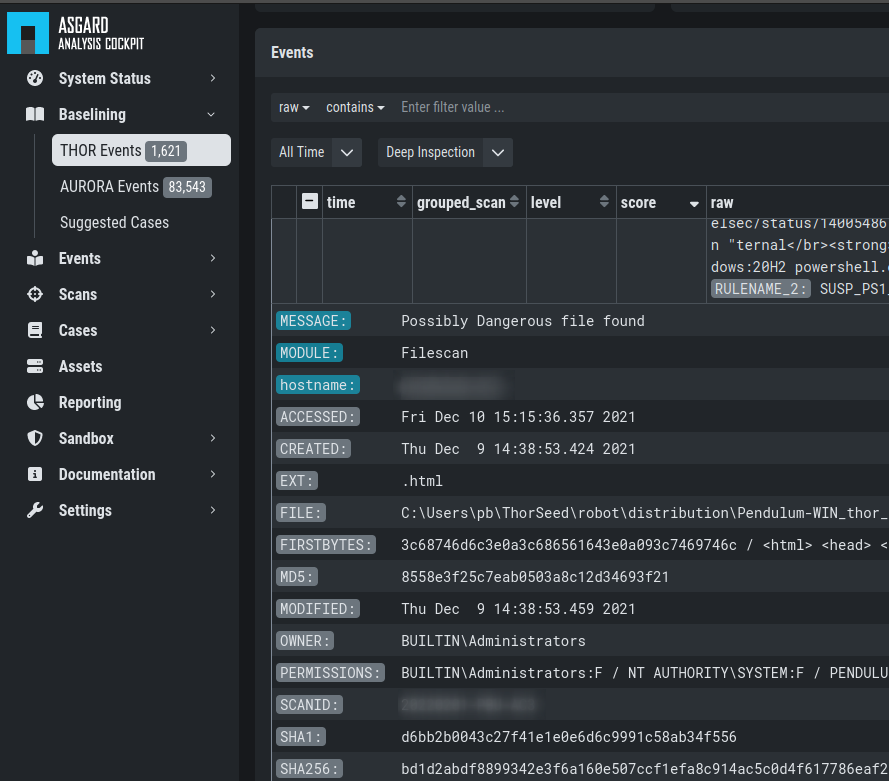
Baselining Section
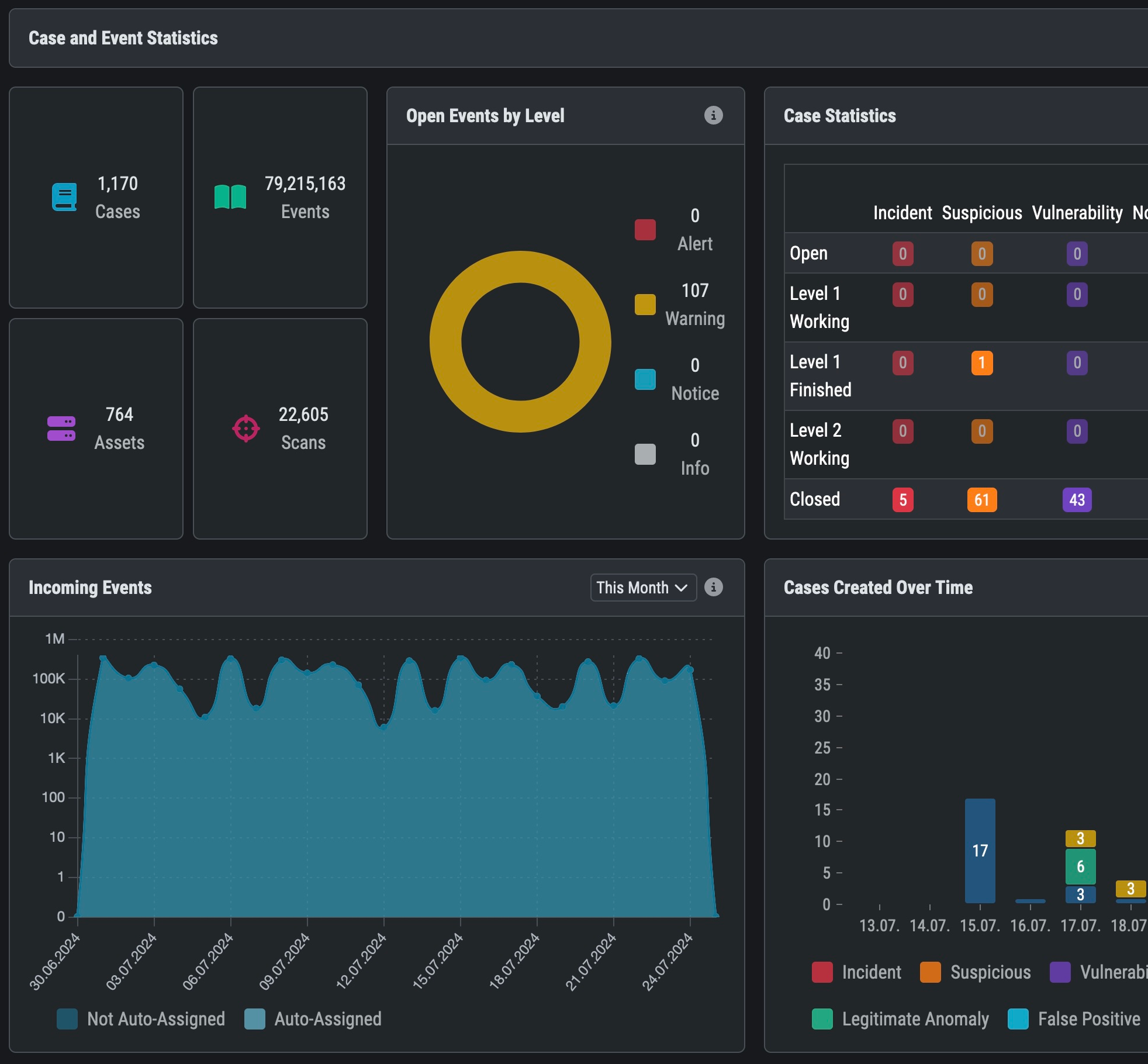
The Baselining Section contains all IOC matches that are not part of an existing baseline – in other words: logs that need to be looked at. Powerful visualisation, filtering and integrated tools like auto grouping help you analyse and categorize your matches and set a new baseline. With “Auto Cases” you can set your baseline with just one click – storing all matches in meaningful groups within the case management section for further analysis.
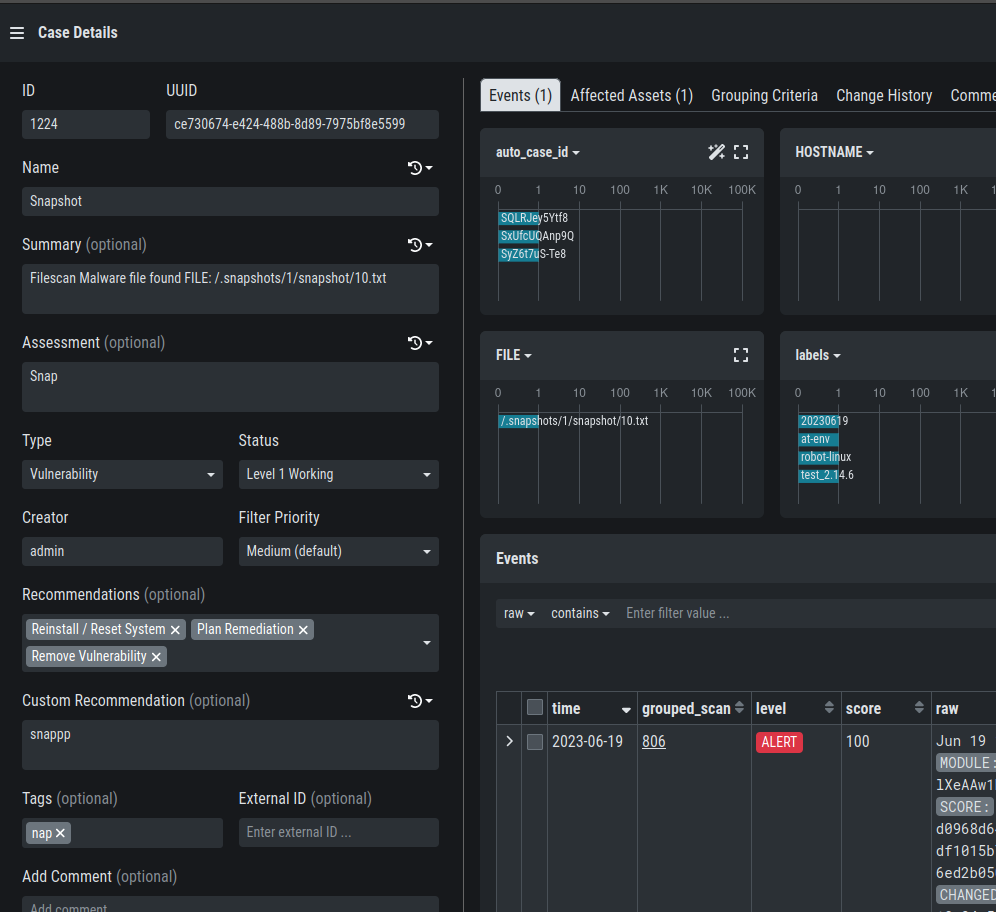
Integrated Case Management
The integrated case management provides an easy to use interface that lets multiple analysts collaborate on the same set of IOC matches. It is highly configurable and supports customizable workflows for multiple analyst groups. The built in two-level analyst model can easily be scaled up to support a multi-level follow the sun SOC. Instead of using the cockpits built-in case management, organisations may decide using the cockpits rich set of APIs to allows handling cases within existing trouble ticket systems, SOAR platforms or within “The Hive”.
Powerful APIs
The Analysis Cockpit features a rich set of APIs for case management, threat intel and sandbox integration. They let you interconnect to trouble ticket- and action request systems, SOAR Systems, “The Hive” and comparable entities. Furthermore the threat intel API connects to threat Intel platforms like Virustotal, MISP and AV vendors. Finally the cockpit APIs let you drop samples into various sandboxes and retrieve respective reports for further analysis.
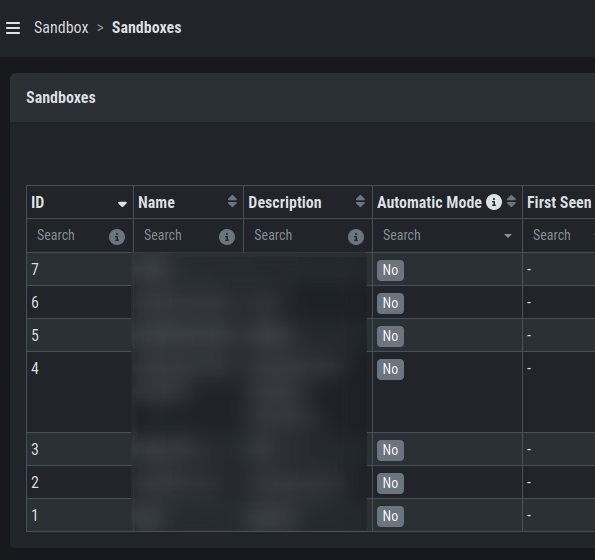
Sandbox Integration
Sample that have been collected by THOR or ADGARD will be stored on the Analysis Cockpit for further investigation. Once a sandbox is connected to the Analysis Cockpit, all samples will be dropped into the sandbox and reports will be retrieved automatically. The Analysis Cockpit ships pre-configured for cuckoo sandbox and with an easy to use API in order to connect to other sandboxes. It is even possible to connect to multiple sandboxes at the same time.
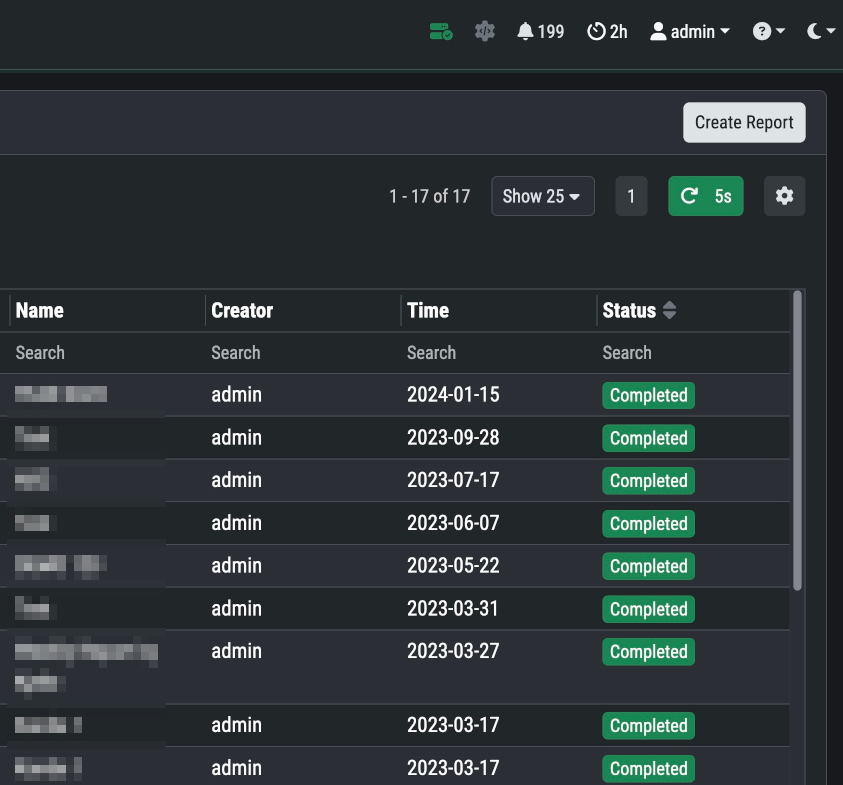
Rich Reporting Section
The reporting section features multiple built-in reports on IOC matches and case management activity. They provide general statistics on all activities and events within the cockpit, help identify lateral movement and hidden threats. Furthermore they help you improve your organisation by providing KPIs for your implemented workflow. Custom reports can be defined and scheduled. External reporting engines can be connected through scheduled exports raw report data.
Incident Response Platform
ASGARD Management Center allows you to configure, schedule and control scans on up to 25,000 end points per instance; It also features an IOC management as well as many response functions.