Notes on VirusTotal Matches
With the courtesy of VirusTotal, we apply a reasonable part of our YARA rule set to the samples uploaded to VirusTotal and post comments to mark these samples and publish some context to help analysts and other researchers.
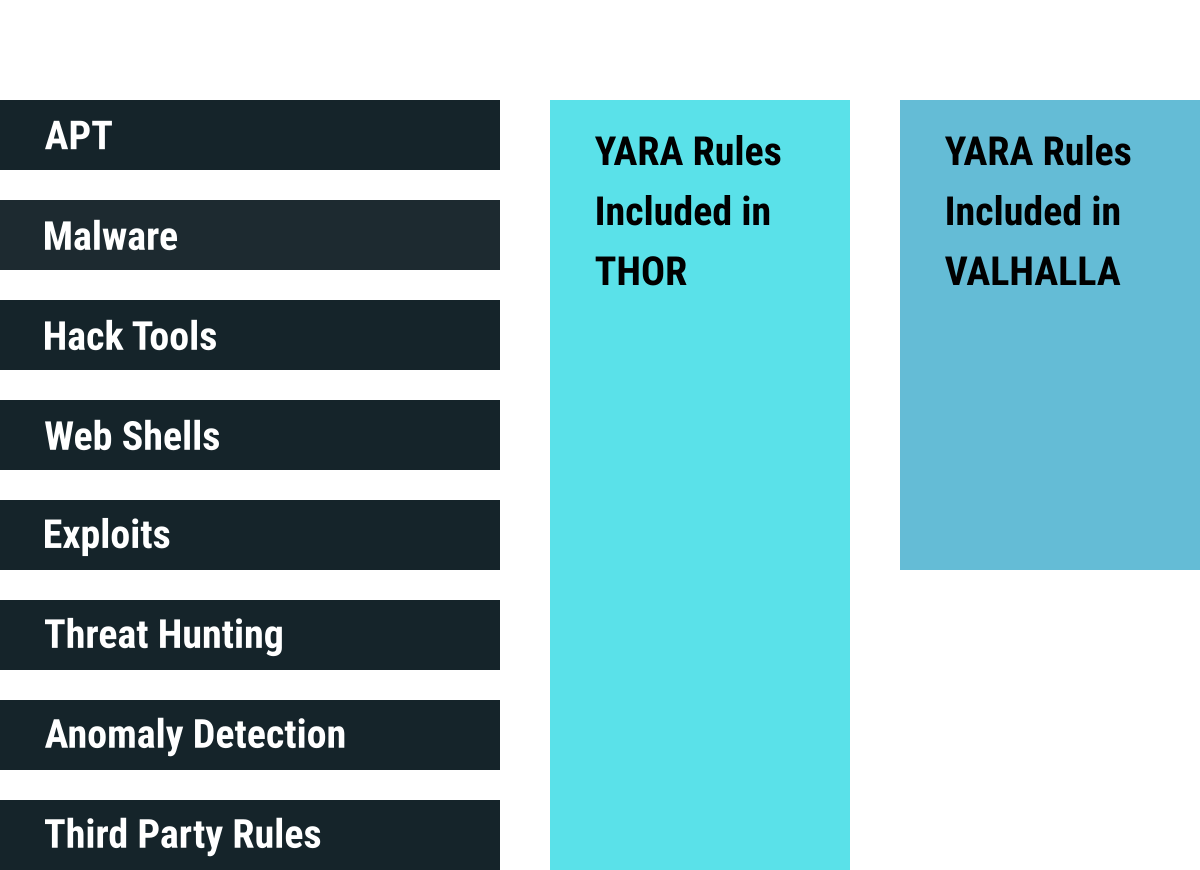
We use the full YARA rule set in our flexible and portable endpoint scanner THOR.
You can supercharge your own detection engine with our rule set using VALHALLA.
Information Regarding the Comments on VirusTotal:
Sub Set
Not all of THOR’s signatures are integrated into VirusTotal. We’ve integrated ~50% of our signature set.
About 20% of THOR’s rules are available as an open source signature database and shipped with the free and open source scanner LOKI and THOR Lite.
Internal Research
‘Internal Research’ means that we have created the rule based on generic characteristics or do not want to share the reference.
Keywords
Special Keywords used in rule names
- “Generic” indicates a rule for a generic string or byte code sequence
- “SUSP_” means that it a rule for a an indicator that is not a hard match and should be treated as “suspicious”
- “APT_” indicates that a rule has been created for a sample in a report for a certain threat group.
- “MAL_” stands for malware
- “HKTL_” stands for hack tools
- “Imphash_” for a rule that looks for known malicious PE import hashes
- “_Combo” means that a combination of keywords triggered the rule
Anomaly Rules
The anomaly category contains the most extraordinary set of rules for anomaly, obfuscation and suspicious indicator detection. (Schemes: *_Anomaly, SUSP_*)
It is not available in VALHALLA anymore but shipped with THOR for threat hunting on endpoints or lab stations.
The rules are often highly generic and able to detect yet unknown threats. It contains rules for casing anomalies, for encoded keywords, rare executable packers, PE header data anomalies and other obfuscation techniques.
Empty Fields
An empty ‘Reference’ or ‘Description’ field means that the reference table for that rules has not been uploaded yet or our internal rule name diverged from the rule name on VirusTotal.
It is a common error that appears in most cases only for a certain amount of time in which the meta data has not yet been synced between our databases. (could be days)
List of Matches
See THOR’s VirusTotal page for all new matches.
Score
The ‘Score’ is a sub score used in THOR to calculate a total score based on all YARA rule matches and other IOC matches (e.g. filename IOC match)
The score ranges between 40 and 100, while 40 is used for very generic and low certainty threat hunting rules and 100 for the highest certainty.
Rule Type
The field ‘Rule Type” states if the rule is a rule that can be found in the open source signature base (shown as “community”) or is one of the privately offered rules in our Valhalla YARA feed service (shown as “VALHALLA rule feed only”).
Attribution
A rule named e.g. ‘IronTiger_Sample1_Apr17_1’ was created from a sample of an ‘Iron Tiger’ report processed in April 2017.
A match shouldn’t be regarded as clear indicator for ‘Iron Tiger’ activity as it may cover a tool or malware that is used by other groups as well.
THOR is our full-featured, portable and flexible compromise assessment scanner for Windows, macOS and Linux systems.
Boost your detection capabilities with the power of thousands of hand-crafted high-quality YARA and Sigma rules.