We are proud to announce the integration of our private Sigma rule set in Valhalla. This rule set is used in our scanner THOR and endpoint agent Aurora. The rule set currently contains more than 250 quality-tested and generic rules written by Nextron's detection...
Sigma Scanning with THOR
Our compromise assessment scanner THOR is able to apply Sigma rules during the local Eventlog analysis. This can help any customer that has no central SIEM system or performs a live forensic analysis on a system group that does not report to central monitoring. By...
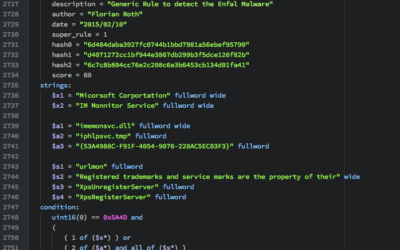
How to Write Simple but Sound Yara Rules – Part 2
Months ago I wrote a blog article on "How to write simple but sound Yara rules". Since then the mentioned techniques and tools have improved. I'd like to give you a brief update on certain Yara features that I frequently use and tools that I use to generate and test...
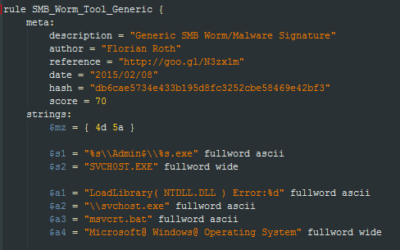
How to Write Simple but Sound Yara Rules
During the last 2 years I wrote approximately 2000 Yara rules based on samples found during our incident response investigations. A lot of security professionals noticed that Yara provides an easy and effective way to write custom rules based on strings or byte...