We are currently upgrading our update infrastructure in many different ways.
We have added 2 new dedicated update servers – update1 (Karlsruhe, Germany) and update2 (Lenexa, USA). The old update locations will still be supported for a few months but have to be regarded as obsolete.
As a customer, please make sure to allow the following update servers in your proxy / firewall:
- update1.nextron-systems.com (443/tcp)
- update2.nextron-systems.com (443/tcp)
In this regard, our old utility called “thor-upgrade.exe” will be out-of-support by the end of July 2018.Please make sure to use the “THOR util” for all update tasks.
Major changes:
- Supports all download types (THOR, SPARK for Windows, Linux, macOS)
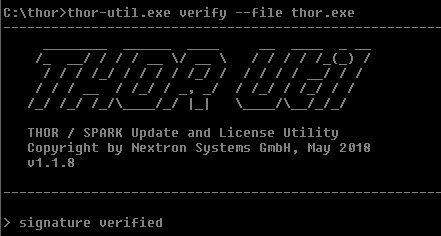
- Verifies Download via RSA signature
- Runs on all platforms (Windows, Linux, macOS)
- Allows updates and the download of a full program packages with config files
- No support for proxy NTLM authentication
It is already part of all download packs.
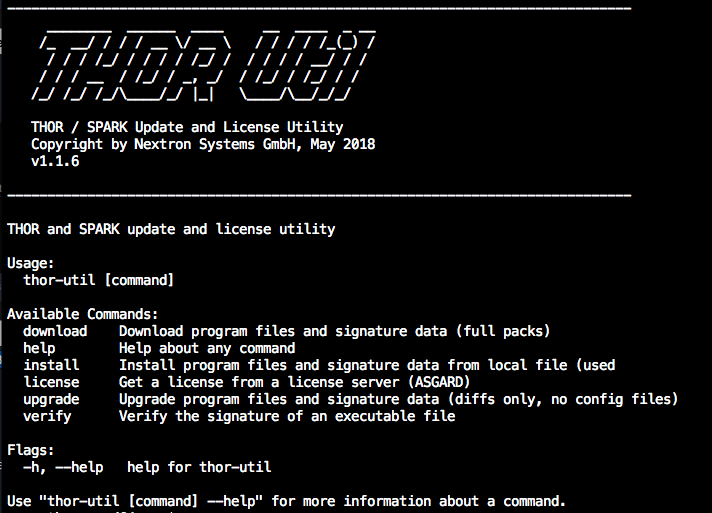
The new version 1.1.6 of THOR util checks the signatures during the upgrade / download and interrupts the process if an invalid signature is found.
If you have any question, don’t hesitate to contact us via support@nextron-systems.com