We are excited to announce the release of ASGARD Analysis Cockpit v4.1, a substantial upgrade from version 4.0. This latest version introduces significant improvements and new features designed to enhance performance, usability, and stability. ASGARD Analysis Cockpit...
Detecting Web Shells: Why it is important to add an additional layer of protection on your existing security solutions
Understanding the importance of web shell detection is crucial in today’s cybersecurity landscape. Traditional antivirus solutions often fall short, but specialized tools like Nextron’s THOR APT scanner provide advanced protection against these stealthy threats, ensuring comprehensive security.
THOR’s Power Unleashed: Multi-Threading for the Masses
We're excited to announce a significant update to THOR, our comprehensive digital forensic scanner, which now extends multi-threading capabilities to both the standard version and THOR Lite. Previously exclusive to our forensic lab license holders, this enhancement...
Protecting Your Business: Addressing the Microsoft Exchange Vulnerability Crisis
Discover how to safeguard your business from the ongoing Microsoft Exchange vulnerability crisis highlighted by the German Federal Office for Information Security (BSI). Learn about critical warnings, the importance of patching, and how automated compromise assessments with THOR Cloud Lite can fortify your cybersecurity strategy.
Tales Of Valhalla – March 2024
Every month the Nextron Threat Research Team (NTRT) shares insights into evasive threats that we’ve seen in the wild via our Valhalla service. The aim is to highlight interesting samples our rules detected and have or had very low detection rates as reported by...
Supercharging Postfix With THOR Thunderstorm
Have you already heard about THOR Thunderstorm, a self-hosted THOR as a service? In this blog post, we will show how you can leverage THOR Thunderstorm to level up your email infrastructure security.THOR Thunderstorm is a web API wrapped around THOR, which accepts...
Integration of THOR in Velociraptor: Supercharging Digital Forensics and Incident Response
Digital forensics and incident response (DFIR) are critical components in the cybersecurity landscape. Evolving threats and complex cyber-attacks make it vital for organizations to have efficient and powerful tools available. If you are not already enjoying the...
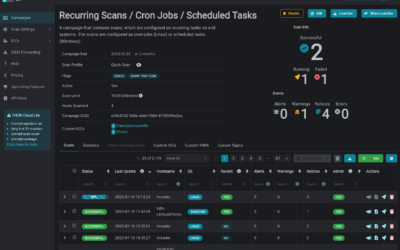
Introducing THOR-Cloud Lite: Seamless On-Demand Forensic Scanning Made Easy
We just launched THOR-Cloud Lite our new free, lightweight and easy to deploy on-demand compromise assessment scanner. Allowing you to access your scans and reports from everywhere at any time. Licensing, scan campaigns and reports everything is conveniently managed...
Mjolnir Security: Incident Response Training – Dive Deep into Cybersecurity
We're thrilled to announce an exciting collaboration with our esteemed partner, Mjolnir Security. Immerse yourself in their renowned “Blue Team Incident Response Training” taking place from the 23rd to the 26th of October. This four-day intensive program promises a...
How to scan Ivanti Endpoint Manager Mobile (EPMM) / MobileIron Core for CVE-2023-35078 Exploitation
In this blog post, we address a critical security concern and explore methods for evaluating potential compromises on devices like Ivanti Endpoint Manager Mobile (EPMM) / MobileIron Core using THOR or the free THOR Lite YARA and IOC scanners. Recently, a severe remote...
How to Perform Compromise Assessments on NetScaler / Citrix ADC Appliances Using THOR
In today's interconnected world, cyber adversaries are increasingly targeting and exploiting Internet-facing appliances and devices with unconventional or restricted operating systems. A pressing concern for users is whether it's possible to perform a compromise...
New THOR 10.7.8 TechPreview Features
We are thrilled to unveil THOR 10.7.8, the latest version of our advanced persistent threat (APT) scanner, which brings a host of powerful features to enhance threat detection and analysis. In this blog post, we will highlight some of the notable additions that make...