Digital forensics and incident response (DFIR) are critical components in the cybersecurity landscape. Evolving threats and complex cyber-attacks make it vital for organizations to have efficient and powerful tools available. If you are not already enjoying the benefits of our ASGARD platform and if your are using Velociraptor for DFIR it is worth to read on. In this blog post, we explore the integration of THOR into Velociraptor and the benefits it brings to Velociraptor users.
If you are a technical reader and already know your way around THOR and Velocriaptor you might want to directly jump to the end of the blog.
DFIR Platforms
If you’re content with Velociraptor for your endpoint management and wary switching your DFIR platform, we understand your concerns. Hence, we’ve crafted artifacts to integrate THOR, our endpoint scanner, into your existing Velociraptor setup. This integration allows you to leverage THOR’s robust scanning capabilities, ensuring a streamlined, efficient, and non-disruptive addition to your security infrastructure. While we consider ASGARD to be the prime solution for managing and evaluating THOR scans, this blog ensures you have a robust alternative that complements and enhances your current security measures without adopting a new platform.
Velociraptor - Digging Deeper!
“Velociraptor is an advanced digital forensic and incident response tool that enhances your visibility into your endpoints.”
https://docs.velociraptor.app/
Velociraptor is a open-source digital forensic and incident response tool designed to collect, monitor and hunt within your environment. At its core is the Velociraptor Query Language (VQL), a solid framework that allows for the creation of highly customized queries. These queries can be used to collect and monitor data from single or multiple endpoints across a network. VQL queries can be packed into ‘Artifacts’, which are structured YAML files containing named queries for easy searching, execution and sharing with the community. These Artifacts serve as modules, each typically focused on retrieving a specific type of information from an endpoint, which simplifies forensic and monitoring tasks.
THOR APT Scanner
THOR is an advanced compromise assessment tool specifically designed to detect hack tools, backdoors, and traces of hacker activities on endpoints that standard Anti-virus solutions often miss. Using over 20,000 YARA signatures and over 24 specific modules, THOR examines systems for signs of attacker tools, system manipulations, and suspicious log activities. THOR has an extensive detection rate, ensuring system stability by monitoring resources and auto-adjusting performance.
Supercharge Your DFIR with Integration
Consider a scenario where you see unusual network activity from a host within your company network. Now, where do you start?
This is where THOR shines: With its huge (offline) detection set, it is perfect to start your DFIR process. With THOR you do not need to know what you are looking for, THOR knows on its own! Use the opensource Velociraptor THOR artifact (see below) to boost your triage while still working in your familiar Velociraptor UI, using its features for collection, monitoring and mitigation.
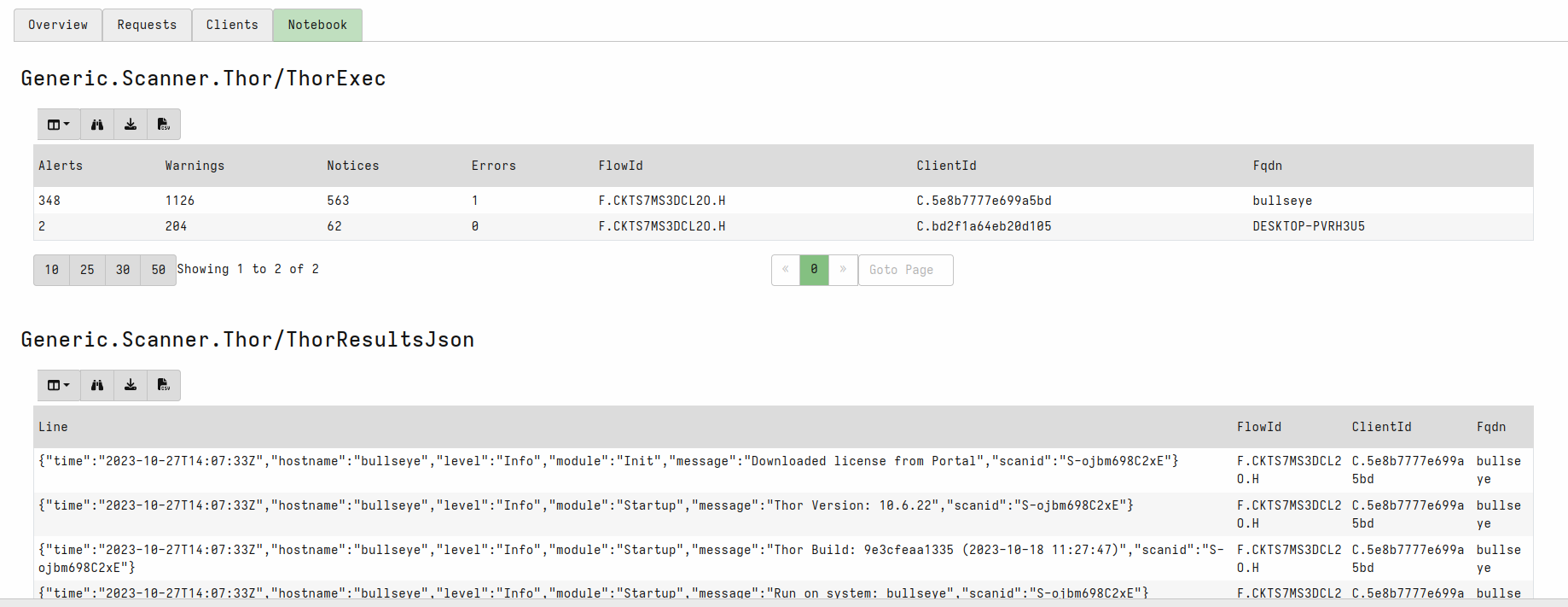
Velociraptor THOR Artifacts
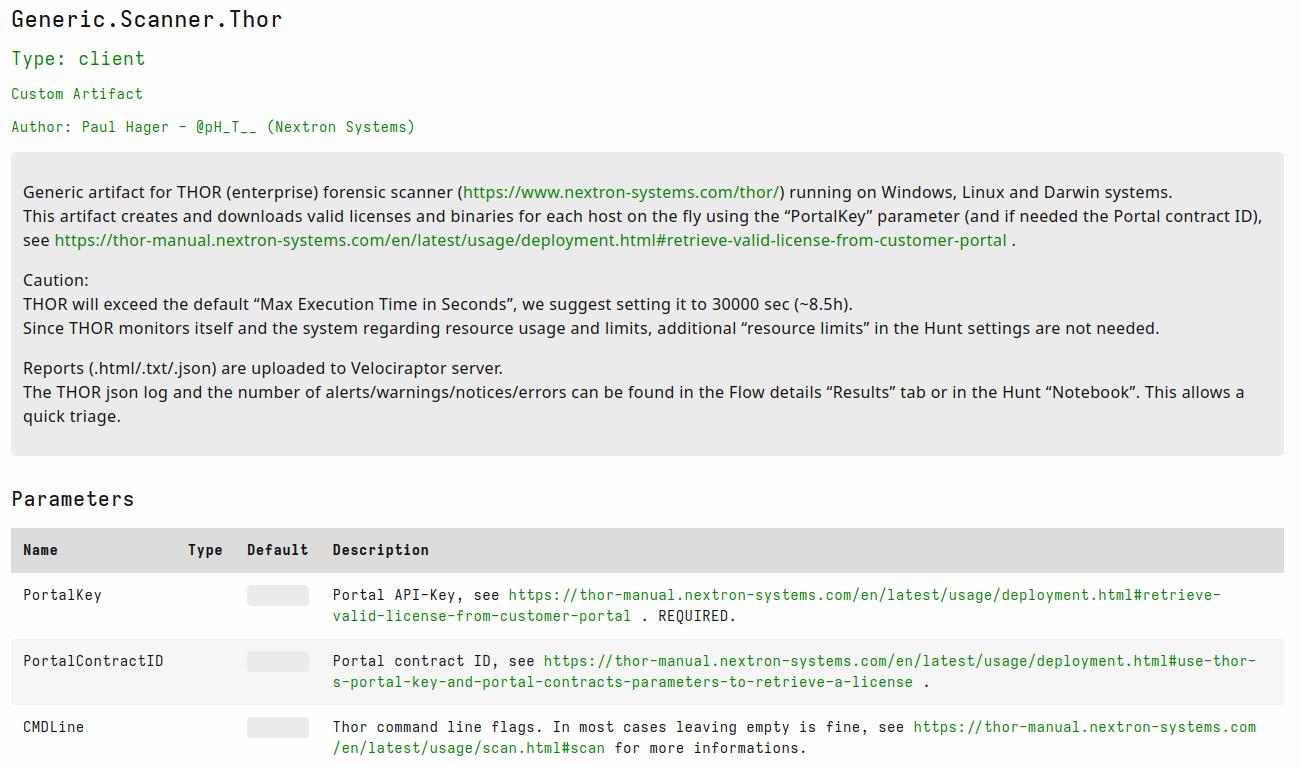
We’ve created three Velociraptor artifacts for using and leveraging THOR:
- Generic artifact for THOR (enterprise) forensic scanner. Works for all major operating systems and licenses endpoints on the fly.
- Artifact which is used best in combination with THOR Lite. Expects a ZIP file with THOR Lite (as downloaded from our servers) and a THOR Lite license. Works for all major operating systems.
- Artifact for our newest member in the THOR family: THOR Cloud
Get Started
To get up and running with Velociraptor and THOR see the following links: