Since we’ve decided to migrate many of the HAFNIUM / Exchange vulnerability related signatures into the open source signature database of our free scanner THOR Lite, both users of the free and the commercial version started asking questions of coverage and if a scan of the respective other version is still recommended.
This blog post tries to shed some light on the issue by pointing out the differences between both scanners regarding coverage, scan intensity and availability of signatures.
The obvious advantage of THOR Lite – which is usually one of the disadvantages – is the immediate availability of untested new YARA signatures. While users usually prefer tested signatures that won’t cause hundreds or thousands of false positives, in case of the ProxyLogon vulnerability, new releases of rules cannot be fast enough.
So the obvious and only advantage of THOR Lite is that it receives rule updates multiple times a day, while THOR currently gets new signatures every 1-2 days.
The signature release schedule is as follows:
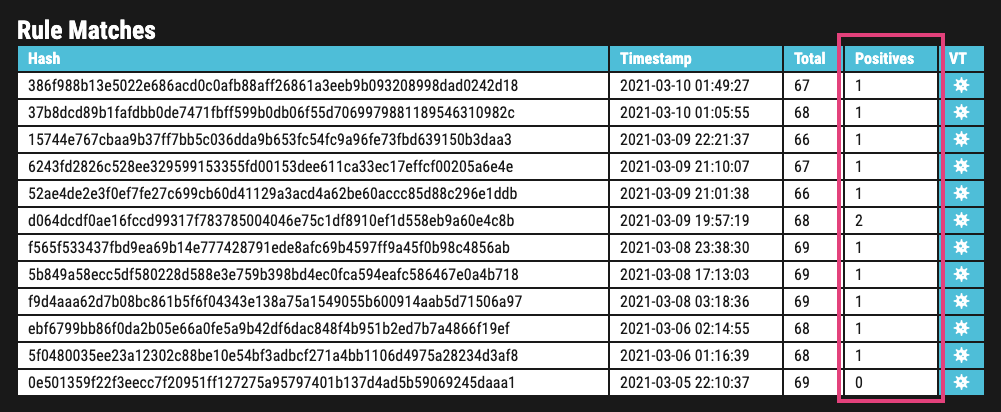
- THOR Lite (untested): on every commit in the repository
- VALHALLA (goodware tested): once per day
- THOR (goodware tested, full CI tests on 20+ operating systems): currently every 1-2 days, normally 1 per week
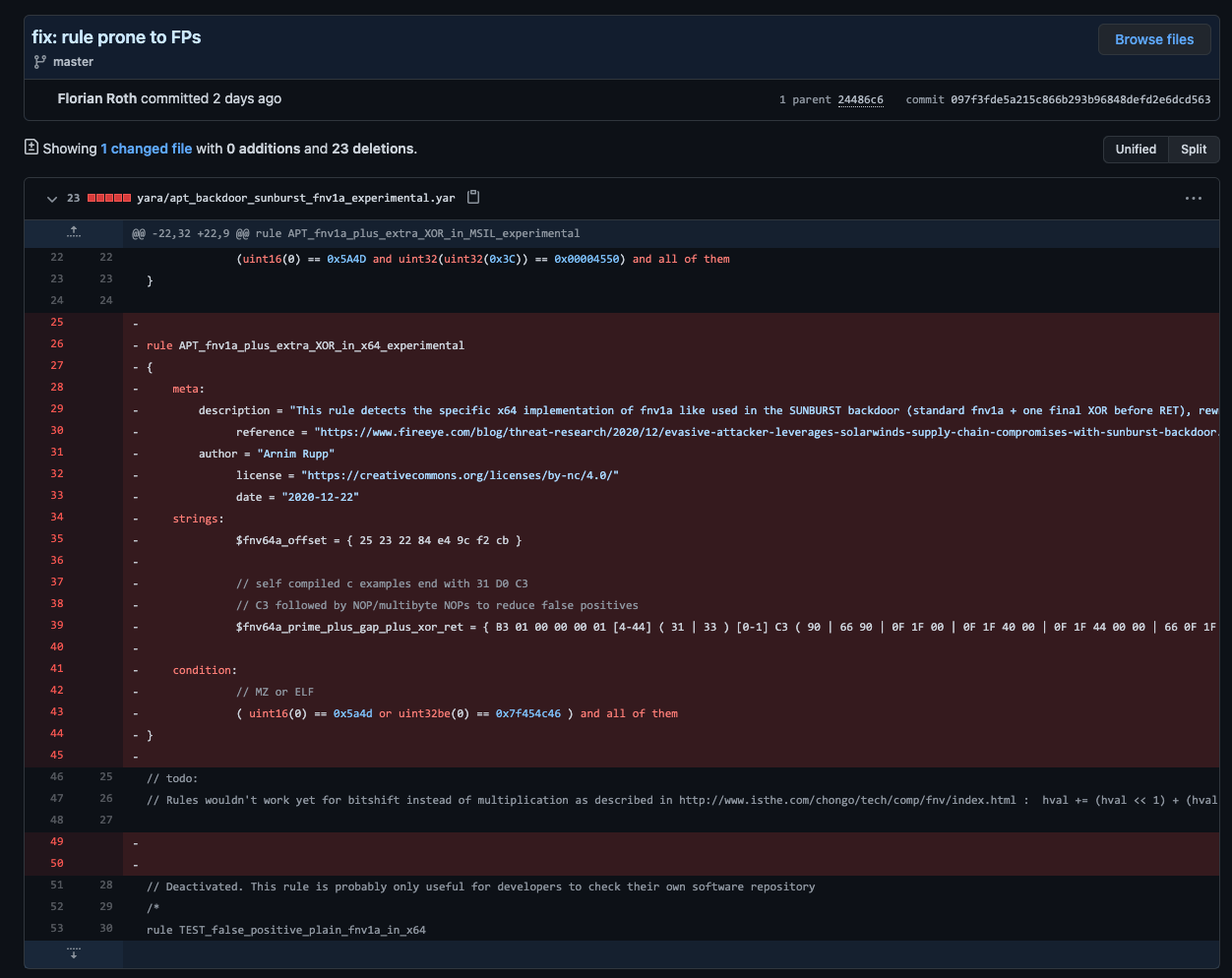
A good example of a rule that caused several false positives and, as a consequence, some trouble is an experimental rule named APT_fnv1a_plus_extra_XOR_in_x64_experimental, which even triggered on files from the Microsoft software catalogue.
It has never been quality tested and has only been in the community signature set used in THOR Lite.
Since we just extend our coverage with every new signature, users who use the ruleset released on Monday the 8th should at least see all different types of exploitation attempts, successful or unsuccessful. They also see many types of web shells, old and new, tools like PowerCat and Nishangs PowerShell one-liner as well as LSASS process memory dumps and other more generic indicators.
So both scanners provide a reasonable coverage and should indicate a successful attack.
THOR may not have the newest signatures, but it provides the bigger rule set with many generic signatures for all kinds of malicious activity, including post-exploitation activity. The following list tries to cover the advantages of a THOR scan in contrast to a THOR Lite scan.
Undisclosed Signatures
We have included many rules in the open source signature set that we use for LOKI and THOR Lite, but not all of them. As stated in a previous post, we have kept some of the more elaborate ones secret to avoid attackers evading the detection in future attacks.
These rules include detection for specific forensic evidence that is often still present on a once compromised system even when the attackers have already removed the previously dropped web shells.
This rule e.g. looks for compiled DLLs that we believe are generated once a dropped web shell gets executed at least once and often resides on a compromised system after the attackers removed their tools, data and web shells.
More Modules, Better Coverage
As you can see in the scanner comparison table, the full THOR version provides many different modules in which it scans different elements of an operating system to discover traces of hacking activity.
We apply many different IOCs like filename patterns, hash values and keywords in these modules to provide the best possible coverage. Find more information on THOR’s IOC scanning in this blog post.
In regards to the HAFNIUM and ProxyLogon activity, we’ve seen enterprise customers with additional findings in
- the Eventlog (Sigma scanning) and
- Scheduled Task module
Other modules that could reveal HAFNIUM activity and are not available in THOR Lite are: MFT, ShimCache, Registry
Better Overall Coverage
The following graph aims to visualise the coverage differences of both scanners only in relation to the HAFNIUM / ProxyLogon activity. In all other cases, the coverage provided by THOR is much higher, since it uses a signature database with more than 14,000 YARA rules and applies these signatures in more than 20 different modules.
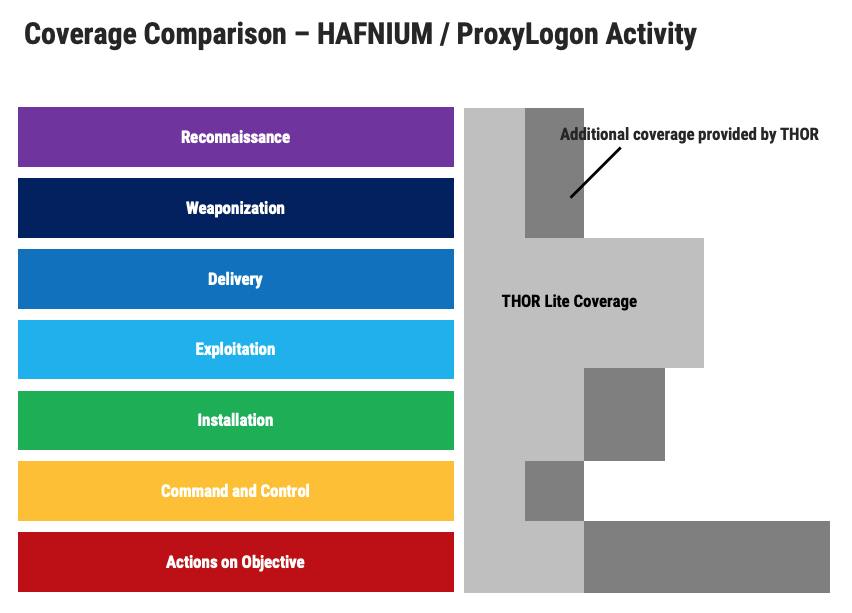
As you can see, especially payloads/evidence used the “delivery” and “exploitation” phase are covered very well by both scanners, but THOR is much better when it comes to detecting post exploitation activity and backdoors or activity other than the described HAFNIUM group activity.
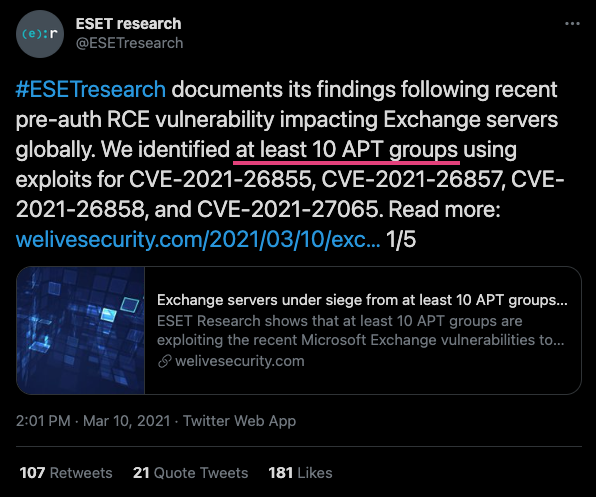
ESET has just recently published a report in which it mentions activity of more than 10 different APT groups.
As this vulnerability attracts more and more threat groups, it gets more and more important to cover as many shells, tools and techniques as possible and widen the view for other actors.
We continue to provide IOCs and signatures regarding that threat in both scanners and also merge rules provided by community members as quickly as possible.