We have received reports from customers that were approached by service providers that offered compromise assessments with our scanner THOR. Subsequently, it appeared, however, that these providers used THOR Lite in their engagements and, when asked about this, argued that THOR Lite would be “just as good as the full version”.
In this article we would like to explain why this is not the case.
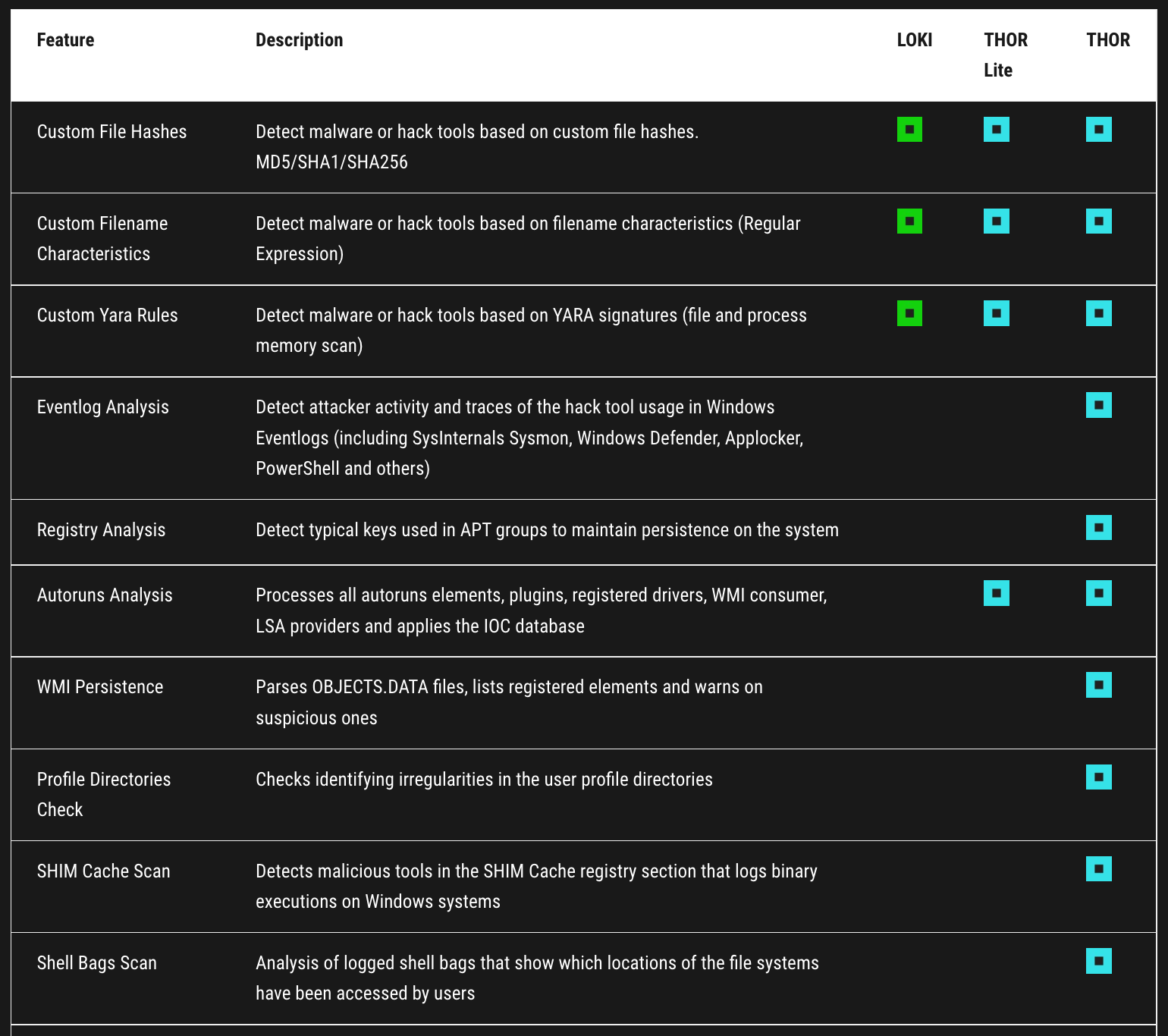
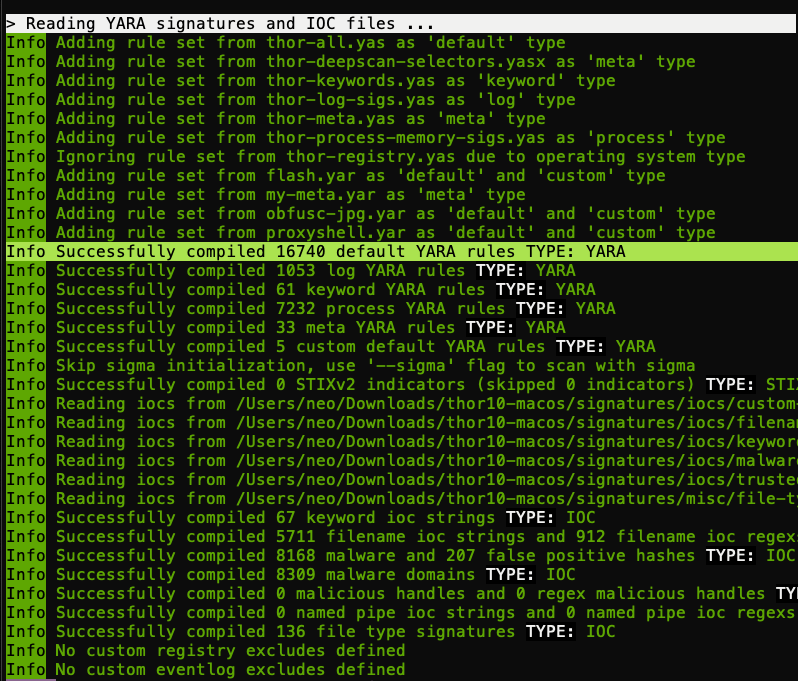
1. The Small Rule Set
The rule set of THOR Lite is much smaller. While THOR uses more than 16,000 YARA rules, THOR Lite only uses the open source signature base, which has ~4000 rules. Of these 4000 rules, 800 are old webshell rules, 300 are written for old Equation Group implants that should be long gone, many others were written for past threat group activity.
Don’t get us wrong – these rules were good at their time and the set contains solid generic rules for some kinds of threats but the effectiveness of the older rules decreases and it is less and less likely that they catch something significant.
The number 4000 compared to 16,000 doesn’t mean that you would still see 1/4 of what THOR is able to detect – honestly, it’s rather 1/30.
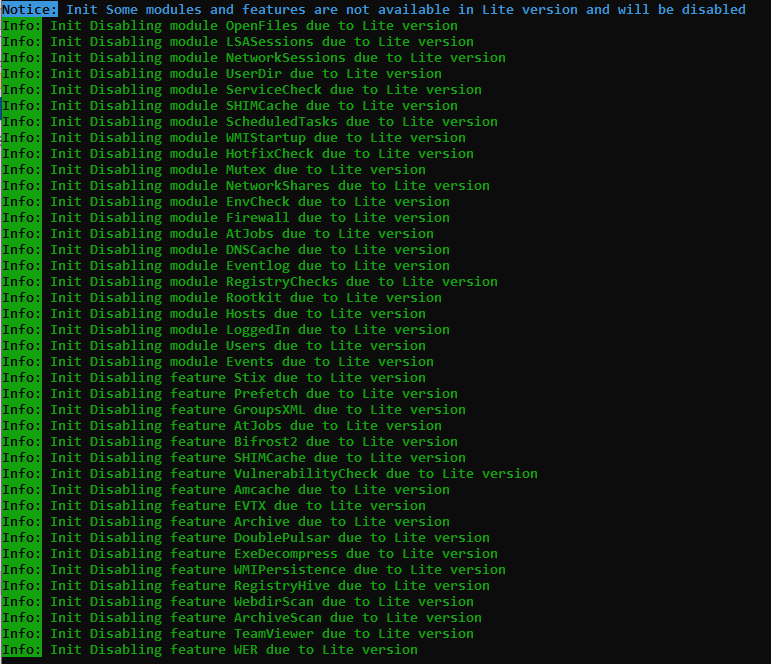
2. The Limited Modules
It is correct that the filesystem often contains evidence, but not traces of adversary activity are not always visible on the filesystem. It’s not unusual that adversaries remove their tools when they’ve finished their job.
Therefore the full version of THOR runs more than 25 modules that look for the IOCs and apply YARA rules in many different locations like the Eventlog, SHIM Cache, Registry and performs checks for hidden implants that can only be identified with their mutex or a handshake on a certain named pipe.
The screenshot on the right shows all disabled modules and features in the Lite version.
Findings in these other modules aren’t just evidence of a compromise but often point to other techniques used by the attackers or other systems that are also affected.
THOR Lite lacks not only depth of visibility with a much smaller rule set but also breadth due to the limited set of modules and features.
The Few Exceptions
There are a few exceptions to the rule of very limited visibility in THOR Lite.
- To showcase what the full version is able to detect, we’ve included all available signatures for the various campaigns against Microsoft Exchange, namely ProxyShell and ProxyLogon. Scanning Exchange servers for this kind of threat is almost as good as using the full version of THOR.
- The few generic detection rules provide a good coverage of common threats, like webshells and crypto miners. Arnim Rupp provided a great set of generic webshell detection rules that are able to highlight new, yet unknown web shells of all kinds (ASP, JSP, PHP etc.).
- The coverage of some well-known hack tools like Mimikatz is also pretty good.
For whom is THOR Lite intended?
THOR Lite is meant as a free community edition to showcase the functionality.
It is meant to be used by private individuals or small organisations without a budget that face common threats like crypto miners and crime groups.
From time to time, we add sets of rules and IOCs to detect dangerous threats with high importance and / or a wide spread – e.g. Exchange vulnerability exploiting, crypto coin miners, Ransomware worms like WannaCry.
Test Drive the Full Version
We recommend a test drive of the full version on compromised or possibly compromised systems to see the big difference in detection capabilities. We also offer affordable license packs for small organisations and give attractive discounts on license packs that are used by IR teams all over the world.
Just use the “get started” contact form and state that you’d like to test the full version of THOR.