It came to our attention that under certain circumstances, after the upgrade to ASGARD 2.11, some ASGARD instances lost their scheduled task to automatically assign the newest signatures to scan jobs . We advice customers to review their update configuration if they...
New Feature: THOR-util and SPARK-Core-util Signature Encryption
The new THOR-util version 1.2.4 supports the encryption of your custom signatures so that you can deploy your own IOC files and YARA rules in an encrypted form. We use a public key in the utilities to encrypt the files for our scanners so that admins, Antivirus...
Write YARA Rules to Detect Embedded EXE Files in OLE Objects
This is the first blog post published on our new website. If you followed my blog on www.bsk-consulting.de you should consider subscribing to the RSS feed of this blog or the "Nextron Systems Newsletter". This is one of the YARA related blog posts showcasing a special...
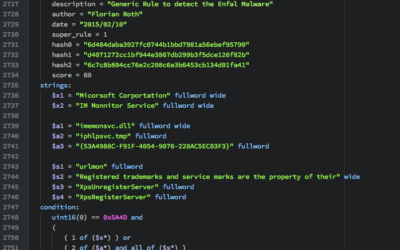
How to Write Simple but Sound Yara Rules – Part 2
Months ago I wrote a blog article on "How to write simple but sound Yara rules". Since then the mentioned techniques and tools have improved. I'd like to give you a brief update on certain Yara features that I frequently use and tools that I use to generate and test...
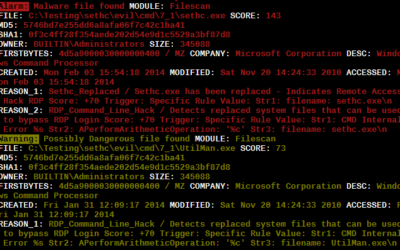
Inverse Yara Signature Matching (Part 1/2)
During our investigations we encountered situations in which attackers replaced valid system files with other system files to achieve persistence and establish a backdoor on the systems. The most frequently used method was the replacement of the "sethc.exe" with the...